Subscribe to P2P-economy
Stay up to date! Get all the latest & greatest posts delivered straight to your inbox
Subscribe
The Institutional Staking Hub is P2P.org's definitive reference for institutions building proof-of-stake programs. From foundational concepts to infrastructure selection and risk architecture, each article addresses a specific operational or technical dimension that determines how a staking program performs in practice.
This is article 2 in the series. Read the foundation first: What Is Institutional Staking? A Complete Guide for Funds, Custodians, and Treasury Teams
What this article covers:
The core argument: Validator infrastructure is not a commodity. The operational decisions made at the infrastructure layer determine uptime, slashing exposure, reward outcomes, and compliance posture. Institutions that treat validator selection as a risk management decision consistently achieve better outcomes than those that treat it as a cost optimisation exercise.
Most institutional conversations about staking start with reward rates. They should start with infrastructure.
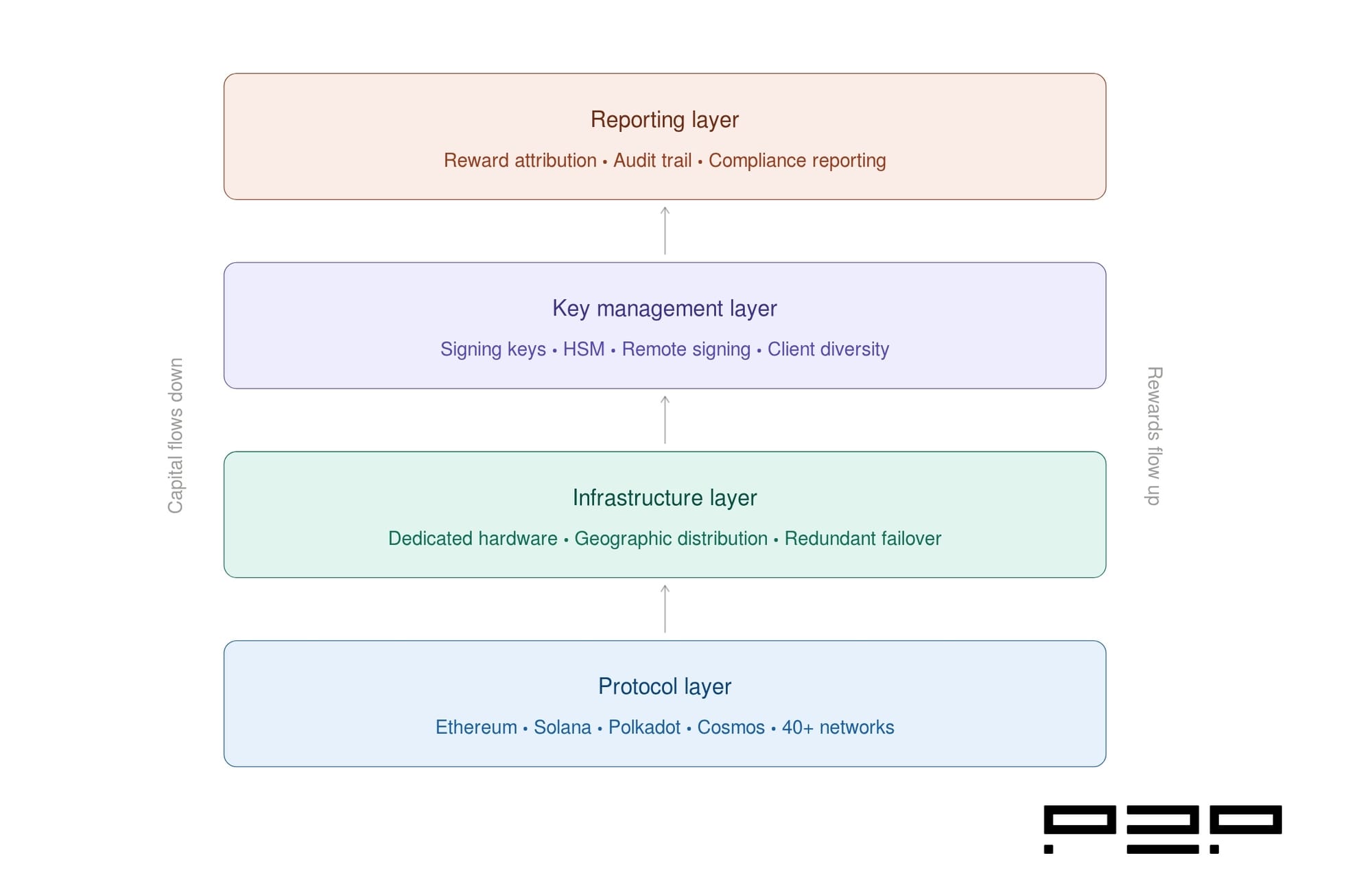
Validator infrastructure is the operational layer that sits between an institution's capital and the proof-of-stake protocol it is participating in. It determines whether consensus participation is reliable or fragile, whether slashing exposure is managed or assumed, and whether the reporting an institution needs for accounting, audit, and compliance can actually be produced.
Major progress in validator infrastructure, institutional custody, multi-chain staking frameworks, and enterprise-grade reporting has made staking operationally viable at scale. For large asset managers, including pension funds, endowments, and conservative allocators, the legal uncertainty and operational risk that kept them on the sidelines are now falling away (Source: CoinShares).
But operational viability is not the same as operational quality. As institutions move from evaluation to deployment, the question changes from whether staking is viable to whether the infrastructure underpinning a specific staking program meets institutional standards. This article answers that question from the ground up.
In a proof-of-stake network, validators are the entities responsible for proposing and attesting to new blocks. They do not just hold staked capital. They run software, maintain network connections, sign messages, and participate in consensus rounds continuously. When a validator goes offline, misses attestations, or double-signs a message, the protocol responds with penalties. When a validator performs correctly, the protocol distributes rewards.
Validator infrastructure is everything that makes that participation happen reliably: the hardware or cloud architecture the validator software runs on, the key management system that controls signing credentials, the monitoring stack that detects and responds to anomalies, the client software that communicates with the network, and the reporting layer that captures everything for downstream use.
Ethereum supports over 1.1 million active validators in 2026, with average validator uptime near 99.2% across the network (Source: CoinLaw). That network average conceals significant variance between operators. In enterprise IT, Service Level Agreements (SLAs) define the expected uptime and reliability of a service provider. The blockchain space is increasingly moving in the same direction, especially as institutions explore staking as part of their portfolio strategy.
Institutions entering proof-of-stake networks have two structural choices for how they participate at the infrastructure layer.
An institution builds and operates its own validator nodes. It controls the infrastructure, manages the keys, handles software updates, and monitors performance directly. This model gives maximum control and governance participation, but it carries the full operational burden. The institution must maintain the specialised engineering capability, 24/7 monitoring, incident response processes, and protocol expertise required to operate validators safely at scale.
Rather than hiring experts, provisioning hardware or cloud infrastructure, and securing forensic-grade security, institutions using a managed service can get their staking strategy up and running in weeks or less. The inverse is equally true: institutions that choose self-operation must be prepared to build all of that capability in-house.
An institution delegates its capital to a professional validator operator. The institution retains custody of its assets at all times. The provider operates the infrastructure, manages keys, monitors performance, handles upgrades, and delivers reporting. This is the dominant model for institutional participation, as it removes the operational burden while preserving custody control.
The critical requirement in any delegated arrangement is non-custody. In a correctly structured staking-as-a-service model, the validator provider never holds the institution's assets. Assets are not transferred. Delegation happens at the protocol level, and the institution retains withdrawal authority.
Not all validator infrastructure is equivalent. The gap between consumer-grade and institutional-grade validator operations shows up across five technical dimensions.
Institutional validators operate on dedicated hardware rather than shared cloud infrastructure, with redundant power, connectivity, and compute. Professional validators target near-perfect uptime backed by strict SLAs. They utilise low-latency bare-metal hardware, high-throughput connectivity, and optimised client diversity to prevent network-wide bugs from causing local outages. Geographic distribution across multiple data centres reduces single-point-of-failure risk. Active/passive failover mechanisms ensure consensus participation continues through hardware or connectivity incidents.
Validator keys are the most sensitive operational asset in a staking program. There are two key types relevant to institutional operations: the signing key, used to participate in consensus, and the withdrawal key, used to access staked capital and rewards.
In an institutional non-custodial arrangement, the institution retains the withdrawal key at all times. The validator operator manages the signing key through a key management system designed to prevent the signing key from being exposed, duplicated, or used in ways that would trigger double-signing penalties. Hardware security modules, remote signing services, and key sharding approaches are all architectural choices at this layer.
Every proof-of-stake network runs on consensus client software. On Ethereum, multiple independent client implementations exist, including Prysm, Lighthouse, Teku, Nimbus, and Lodestar on the consensus layer. The risk of running a single client in concentration is significant. The Prysm outage in December 2025, where validator participation dropped to approximately 75% and 248 blocks were missed, vividly demonstrated the risk posed by stakers herding toward a single consensus client.
Institutional-grade providers operate diversified client environments. If one client has a bug or outage, validators running alternative clients continue participating normally. This is a meaningful differentiator that does not appear in uptime statistics measured under normal conditions.
Validator infrastructure requires continuous monitoring: block proposal success rates, attestation participation, peer connectivity, signing latency, and software version currency. Institutional-grade operations maintain 24/7 monitoring with defined escalation paths and incident response procedures. To avoid slashing, validators must operate secure, redundant, and highly available infrastructure. This includes implementing slashing protection mechanisms such as remote signing, key sharding, or sentry node architectures, and continuously monitoring node health, block production, and consensus participation metrics.
Institutions need validator-level reward attribution for accounting, tax reporting, and audit purposes. This requires a reporting layer that captures rewards at the epoch level, attributes them to specific delegations, and delivers data in formats compatible with institutional back-office systems. Performance data, slashing history, and governance participation records all require structured capture. This layer is frequently underspecified in evaluations focused on uptime and fee rates.
Distributed Validator Technology (DVT) is a protocol-level mechanism that distributes the validator signing function across multiple independent nodes. Rather than a single node holding and using the signing key, DVT allows a threshold of nodes to collectively produce validator signatures. No single node has access to the complete key.
For institutional operations, DVT addresses two risk categories simultaneously. First, it eliminates single-point-of-failure at the signing layer. A hardware failure, network outage, or compromise of a single node does not disable the validator or expose the signing key. Second, it structurally prevents double-signing, since generating a duplicate signature requires a threshold of nodes to act simultaneously, which does not occur under normal failure conditions.
DVT is not yet universally deployed across all proof-of-stake networks, but its adoption is accelerating on Ethereum and represents a meaningful infrastructure maturity signal when evaluating providers.
Protocol rewards are generated by the network, not by the validator provider. What the infrastructure layer controls is how efficiently those rewards are captured.
On Ethereum, rewards come from two sources: consensus layer rewards (base staking rewards for correct block proposals and attestations) and execution layer rewards (priority fees and MEV). Base ETH staking rewards generally range from 3% to 4%, while restaking incentives can temporarily lift combined yields above 8% to 15% (Source: CoinLaw).
Infrastructure quality affects reward capture in measurable ways. A validator with sustained 99.9% uptime captures consensus rewards on nearly every eligible slot. A validator with 98% uptime misses roughly 1 in 50 attestation opportunities. At scale, that difference compounds into material reward outcomes across a staking program.
MEV capture is a separate infrastructure consideration. Validators connected to MEV relays receive a share of transaction ordering value from block builders. Institutional operators must evaluate the MEV relay landscape for compliance implications, since certain relay types may route transactions in ways that conflict with regulatory obligations around transaction ordering.
Network conditions determine protocol-generated rewards and are variable. P2P.org does not control or set reward rates.
For institutions operating under regulatory obligations, independent validation of validator infrastructure controls matters.
SOC 2 Type II is the most relevant independent security attestation for validator infrastructure providers. Enterprise clients typically want Type II reports because they demonstrate how controls perform in real operations, not just at a point in time. A SOC 2 Type II report covering availability and security criteria provides meaningful independent assurance that the controls governing validator uptime and key management are operating as documented. It is a floor, not a ceiling, but it is a meaningful one. P2P.org achieved SOC 2 Type II certification in December 2025, independently validating our operational controls across security and availability criteria (Source: P2P.org).
ISO 27001 certification for information security management systems is a second relevant attestation, particularly for institutions operating under MiCA in Europe or with data governance obligations. Penetration testing records, incident disclosure history, and governance participation policies round out the compliance picture.
Institutional adoption of crypto risk frameworks has climbed to 78%, with custodial spend reaching $16 billion in 2025. Risk compliance ranks as the top priority for 84% of institutions. CoinLaw Validator infrastructure sits at the centre of that risk framework for any institution running a staking program.
For a complete evaluation process, including the specific questions to ask and the mechanisms to assess, see our Validator Playbook article: Validator Due Diligence: An Institutional Framework.
The criteria below are the foundational dimensions any institutional evaluation must cover.
P2P.org operates non-custodial validator infrastructure across more than 40 proof-of-stake networks, supporting custodians, funds, ETF issuers, and treasury teams with institutional-grade staking programs. Our infrastructure operates on dedicated hardware with geographic distribution, client diversity across consensus implementations, and SOC 2 Type II certification achieved in December 2025.
Institutions retain full custody of their assets throughout. Validator-level reward reporting is available for accounting and audit requirements. Governance participation policies are configurable per delegation.
Explore our infrastructure and supported networks at p2p.org.
Building an institutional staking program? P2P.org provides non-custodial validator infrastructure across 40+ proof-of-stake networks, with validator-level reporting and operational safeguards designed for institutional requirements. Explore P2P.org Staking Infrastructure
Validator infrastructure is the operational foundation of every institutional staking program. It determines uptime, slashing exposure, reward capture, reporting capability, and compliance posture. The decision of which infrastructure to operate or delegate to is a risk management decision, not a cost decision.
The institutions that will operate effective staking programs at scale are those that evaluate validator infrastructure with the same rigour they apply to any other mission-critical operational dependency. The checklist above is a starting point. The standard is set by the protocol and by the expectations of the risk committees, custodians, and regulators that govern institutional capital.
Network conditions determine protocol-generated rewards and are variable. P2P.org does not control or set reward rates. Slashing risks are protocol-defined and client-borne. Operational safeguards are implemented to reduce slashing exposure but do not eliminate protocol-level risk.
Validator infrastructure is the technical stack that enables participation in proof-of-stake consensus. It includes the hardware or cloud architecture the validator software runs on, the key management system that controls signing credentials, the monitoring and incident response stack, the consensus client software, and the reporting layer that captures performance and reward data. Validator infrastructure determines uptime, slashing exposure, reward capture, and compliance posture for any staking program.
In a self-operated model, the institution builds and runs its own validator nodes, retaining full control but carrying the full operational burden, including specialised engineering, 24/7 monitoring, and protocol expertise. In a delegated model (staking-as-a-service), a professional validator provider operates the infrastructure while the institution retains custody of its assets at all times. The delegation happens at the protocol level, and the institution retains withdrawal authority. Most institutional participants use the delegated model.
Institutional-grade validator infrastructure operates on dedicated hardware with geographic redundancy, runs diversified consensus clients to avoid single-client failure risk, manages signing keys through hardware security modules or remote signing services, maintains 24/7 monitoring with documented incident response procedures, holds independent certifications such as SOC 2 Type II, and delivers validator-level reward reporting compatible with institutional accounting and audit requirements.
DVT distributes the validator signing function across multiple independent nodes. No single node holds the complete signing key. A threshold of nodes must act together to produce a valid signature. This eliminates single-point-of-failure at the signing layer and structurally prevents double-signing, since triggering that condition requires a threshold of nodes to act simultaneously under failure conditions. For institutions, DVT is a meaningful risk reduction mechanism at the key management layer.
Protocol rewards are determined by the network, not by the provider. However, infrastructure quality determines how efficiently rewards are captured. A validator with sustained 99.9% uptime captures consensus rewards on nearly every eligible slot. A validator with 98% uptime misses approximately 1 in 50 attestation opportunities. At the institutional scale, that gap compounds into material reward differences over time. MEV relay selection is a separate infrastructure consideration with both performance and compliance implications.
SOC 2 Type II is the most relevant independent certification for validator infrastructure, as it validates how operational controls perform over time rather than at a single point in time. ISO 27001 is relevant for information security management, particularly under MiCA in Europe. Institutions should also request penetration testing records, incident disclosure history, and documentation of governance participation policies as part of their due diligence process.
In non-custodial staking, the institution's assets remain under the institution's control throughout the staking process. The validator provider operates infrastructure but never holds the assets. Withdrawal keys remain with the institution. In custodial staking, assets are transferred to the provider or a third-party custodian, which triggers additional regulatory obligations in most institutional compliance frameworks. Non-custodial architecture is the standard requirement for institutional staking programs because it preserves custody integrity and avoids the regulatory implications of asset transfer.
Disclaimer
This article is provided for informational purposes only and does not constitute legal, regulatory, compliance, or investment advice. Regulatory obligations may vary depending on jurisdiction and specific business activities. Readers should consult their own legal and compliance advisors regarding applicable requirements.
<p><strong>Series:</strong> Institutional Lens | Validation Infrastructure</p><p>The Institutional Lens series unpacks the protocol mechanics, infrastructure decisions, and governance considerations that matter most for institutional participants in proof-of-stake networks. Each article is written for professionals operating at the intersection of traditional finance and blockchain infrastructure, including digital asset custodians, crypto-native funds, ETF issuers, treasury teams, and staking product managers.</p><p><strong>Previously in the series:</strong> <a href="https://p2p.org/economy/why-institutional-capital-needs-a-protection-layer-in-proof-of-stake-networks/">Why Institutional Capital Needs a Protection Layer in Proof-of-Stake Networks</a></p><h2 id="introduction">Introduction</h2><p>Solana has crossed a threshold that changes how institutional participants need to think about it. Total Payment Volume on Solana surged 755% year-over-year, driven by institutional adoption and approximately $950 million in ETF inflows (Source: <a href="https://www.ainvest.com/news/sol-sees-strong-staking-transaction-growth-institutional-interest-2026-2603/?ref=p2p.org">Ainvest</a>). The March 2026 SEC and CFTC joint interpretation explicitly classified SOL as a digital commodity and confirmed that solo, self-custodial, custodial, and liquid staking models do not constitute securities transactions. The regulatory overhang that kept many compliance teams on the sidelines is gone.</p><p>What remains is a decision that carries more institutional weight than most teams have yet appreciated. The question is not whether to stake SOL, but how. For digital asset custodians, crypto-native funds, ETF issuers, treasury teams, and staking product managers, Solana staking for institutions is not a single product. Native staking and liquid staking are structurally different risk profiles, custody architectures, and capital management frameworks. Getting this decision right is as important as the allocation decision itself.</p><h2 id="learnings-for-busy-readers"><strong>Learnings for Busy Readers</strong></h2><p>What this article covers:</p><ul><li>How native and liquid staking differ structurally, not just mechanically</li><li>The risk, custody, and liquidity implications of each for institutional participants</li><li>How the current market shift across ETF approvals, LST fragmentation, and Alpenglow changes the calculus</li><li>A decision framework and due diligence checklist for institutional teams</li></ul><p><strong>The core argument:</strong> Native staking offers full custody control, no smart contract exposure, and a clean compliance posture. Liquid staking offers capital efficiency and DeFi composability at the cost of additional risk layers. For most institutional mandates, the right answer is not one or the other. It is understanding exactly which tradeoffs your organisation is equipped to underwrite.</p><h2 id="the-decision-is-not-what-most-teams-think-it-is">The Decision Is Not What Most Teams Think It Is</h2><p>The most common framing of the native vs. liquid staking question in Solana staking for institutions is a yield question. Native staking currently generates 5 to 7% APY depending on validator performance and commission rates, while liquid staking tokens such as JitoSOL and JupSOL generate between 5.89% and 6.16% APY as of early 2026, with some protocols reaching higher during periods of elevated network activity (Source: <a href="https://sanctum.so/blog/best-solana-yield-2026-staking-vs-defi?ref=p2p.org">Sanctum</a>).</p><p>For retail participants, the yield differential is the dominant consideration. For institutional participants, it is rarely the right place to start. The correct framing is a risk architecture question: what risk layers is your organisation prepared to accept, and does your mandate permit them?</p><p>Native staking and liquid staking expose participants to materially different risk categories. Understanding those categories, not the APY differential, is the foundation of a defensible institutional staking framework on Solana.</p><h2 id="native-staking-the-institutional-baseline">Native Staking: The Institutional Baseline</h2><p>In native staking, SOL is delegated directly from a client-controlled wallet to a validator. The delegator retains full custody of the private keys. The staked SOL never leaves the delegator's control. It is locked for voting weight purposes, not transferred to a third party.</p><p><strong>What native staking provides for institutions:</strong></p><p><strong>Full non-custodial architecture.</strong> The validator never holds client assets. Delegation is an instruction, not a transfer. This is structurally aligned with the non-custodial infrastructure model that institutional compliance frameworks typically require.</p><p><strong>No smart contract risk.</strong> Native staking operates at the protocol layer. There is no additional smart contract between the delegator and the network. The only code risk is Solana's base layer itself.</p><p><strong>Clean regulatory posture.</strong> The March 2026 SEC and CFTC interpretation explicitly confirmed that self-custodial staking with a third-party validator, where the custodian acts as agent and does not determine staking amounts or fix reward rates, is not a securities transaction. Native staking maps directly to this definition.</p><p><strong>Predictable reward mechanics.</strong> Protocol-generated rewards accrue each epoch, approximately every two days, are denominated in SOL, and compound automatically into the staked balance. Reward rates are determined entirely by network conditions.</p><p><strong>The institutional tradeoff:</strong></p><p>The primary constraint of native staking for institutions is liquidity. Native staking locks SOL for approximately two epochs, around four to five days, when unstaking is initiated (Source: <a href="https://hittincorners.com/guides/solana-liquid-staking-complete-guide-2026/?ref=p2p.org">HittinCorners</a>). For treasury teams managing redemption obligations or funds with liquidity covenants, this is a material consideration. It is not a disqualifying one, but it needs to be accounted for in position sizing and liquidity management frameworks before capital is deployed.</p><p>The secondary consideration is validator selection. In native staking, the delegator chooses a specific validator. That choice has direct implications for reward performance, slashing risk exposure, and governance representation. It is an active decision that requires due diligence, not a passive one.</p><h2 id="liquid-staking-capital-efficiency-with-additional-risk-layers">Liquid Staking: Capital Efficiency with Additional Risk Layers</h2><p>In liquid staking, SOL is deposited into a staking protocol such as Jito, Marinade, or Sanctum, which delegates to a set of validators and issues a liquid staking token (LST) representing the staked position plus accrued rewards. The LST can be traded, used as collateral in DeFi protocols, or swapped back to SOL through liquidity pools.</p><p>Over $3.3 billion in SOL is liquid-staked across Jito, DoubleZero, Marinade, and Sanctum as of early 2026, representing approximately 10 to 15% of all staked SOL. The segment is growing rapidly and is increasingly the focus of institutional product development.</p><p><strong>What liquid staking adds for institutions:</strong></p><p><strong>Liquidity.</strong> LSTs can be swapped back to SOL near-instantly through liquidity pools, removing the epoch lock-up constraint of native staking.</p><p><strong>DeFi composability.</strong> LSTs can be used as collateral on lending protocols, provided as liquidity in AMM pools, or deployed in structured yield strategies. This unlocks additional reward layers on top of the base staking rate, a meaningful consideration for institutions seeking to maximise capital efficiency.</p><p><strong>MEV distribution.</strong> Protocols like Jito pass a portion of MEV block tips to LST holders, which is why JitoSOL consistently generates a modest premium above the base native staking rate.</p><p><strong>The institutional risk calculus:</strong></p><p>Liquid staking for institutions introduces risk categories that native staking does not. Every institutional team evaluating LSTs needs to assess these explicitly.</p><p><strong>Smart contract risk.</strong> The LST protocol itself is a smart contract. Vulnerabilities in that contract represent a risk to staked capital that does not exist in native staking. The relevant question is not whether a protocol has been audited, as most have been, but whether your mandate permits smart contract exposure at all, and whether the protocol's audit history and incident record are acceptable to your risk committee.</p><p><strong>LST depeg risk.</strong> Under market stress, LSTs can trade below their underlying SOL value. During periods of stress, LSTs can trade below their underlying asset value. Institutions should maintain sufficient liquidity buffers and avoid over-leveraging LST positions (<a href="https://www.cobo.com/post/liquid-staking-for-institutions-complete-mpc-infrastructure-guide?ref=p2p.org">Cobo</a>). For funds with mark-to-market accounting obligations, a temporary depeg is a profit and loss event regardless of whether the underlying position eventually recovers.</p><p><strong>Validator concentration risk.</strong> LST protocols delegate to validator sets according to their own algorithms. The delegator has no direct control over validator selection. This matters for institutions with specific governance obligations, as they are effectively delegating governance representation to the protocol's delegation strategy rather than making that decision directly.</p><p><strong>Custody and compliance complexity.</strong> LSTs are tokens, not staking positions. Their treatment for accounting, tax reporting, and regulatory classification may differ from native staked SOL depending on jurisdiction. This is an active area of legal development and warrants specific advice for each institution.</p><h2 id="what-is-changing-right-now-and-why-it-matters">What Is Changing Right Now and Why It Matters</h2><p>Three developments in early 2026 have materially shifted the landscape for Solana staking for institutions.</p><p><strong>The SEC and CFTC commodity ruling.</strong> The March 17 joint interpretation formally cleared all four staking models, including liquid staking, as non-securities activities. For compliance teams that had blocked LST exposure pending regulatory clarity, that barrier is now removed. The question shifts from whether an institution can participate to whether it should, and under what framework.</p><p><strong>LST market fragmentation.</strong> JitoSOL's dominance is fracturing. Nasdaq filed a proposal in February 2026 to list the VanEck JitoSOL Solana Liquid Staking ETF, the first attempt to offer a regulated product tied directly to an LST. Galaxy Digital launched institutional SOL staking in March 2026. Hex Trust integrated JitoSOL for custodial staking, signalling that traditional custodians are beginning to treat LSTs as standard yield products. The LST landscape is maturing rapidly, but it is also becoming more complex. Institutions entering now face more protocol choices, more counterparty relationships, and more due diligence surface area than existed twelve months ago.</p><p><strong>Alpenglow's impact on native staking economics.</strong> The Alpenglow upgrade, approved by 98% of validators and deploying in 2026, will eliminate validator voting fees entirely. The elimination of voting fees means validators keep a larger portion of their earnings, effectively making staking more profitable for both validators and delegators, particularly for smaller operators who were previously losing a higher percentage of rewards to mandatory voting costs (Source: <a href="https://phemex.com/blogs/solana-alpenglow-upgrade-finality-explained?ref=p2p.org">Phemex</a>). For institutions in native staking programs, this represents an improvement in net reward rates without any change to risk posture, a meaningful compression of the native vs. liquid yield differential.</p><h2 id="the-institutional-decision-framework">The Institutional Decision Framework</h2><p>This is not a binary choice. Many institutional programs will run both: native staking for their core, compliance-sensitive position, and a controlled LST allocation where the mandate permits and the risk framework supports it. The relevant questions for each component are the following.</p><p><strong>For native Solana staking for institutions:</strong></p><p>Is your custody architecture non-custodial and client-controlled? Have you conducted due diligence on your validator's infrastructure, incident history, and governance posture? Is your liquidity management framework designed around the epoch lock-up timeline? Does your reward reporting infrastructure support validator-level attribution for accounting and audit purposes?</p><p><strong>For liquid staking as an institutional layer:</strong></p><p>Does your mandate permit smart contract exposure, and has legal confirmed the applicable standard? Has your risk committee reviewed the specific protocol's audit history, slashing incident record, and depeg history? Does your accounting framework have a defined treatment for LST mark-to-market movements? Are you clear on the tax treatment of LST rewards in each operating jurisdiction? Is the validator governance delegation of the LST protocol acceptable, given that the protocol determines it rather than you?</p><p><a href="http://p2p.org/?ref=p2p.org">P2P.org</a>'s <a href="https://p2p.org/networks/solana?ref=p2p.org">Solana staking infrastructure</a> is built for institutional native staking with non-custodial architecture, validator-level reporting, geographically distributed infrastructure, and operational safeguards aligned with the risk posture institutional partners require. Our <a href="https://docs.p2p.org/?ref=p2p.org">technical documentation</a> provides detailed guidance on integration, reward reporting, and operational architecture for teams building or evaluating a Solana staking program.</p><figure class="kg-card kg-image-card"><img src="https://p2p.org/economy/content/images/2026/05/Native-vs.-liquid-staking-on-Solana-compared-across-custody--smart-contract-risk--liquidity--and-governance-dimensions-for-institutional-allocators..png" class="kg-image" alt="Native vs. liquid staking on Solana compared across custody, smart contract risk, liquidity, and governance dimensions for institutional allocators." loading="lazy" width="1600" height="900" srcset="https://p2p.org/economy/content/images/size/w600/2026/05/Native-vs.-liquid-staking-on-Solana-compared-across-custody--smart-contract-risk--liquidity--and-governance-dimensions-for-institutional-allocators..png 600w, https://p2p.org/economy/content/images/size/w1000/2026/05/Native-vs.-liquid-staking-on-Solana-compared-across-custody--smart-contract-risk--liquidity--and-governance-dimensions-for-institutional-allocators..png 1000w, https://p2p.org/economy/content/images/2026/05/Native-vs.-liquid-staking-on-Solana-compared-across-custody--smart-contract-risk--liquidity--and-governance-dimensions-for-institutional-allocators..png 1600w" sizes="(min-width: 720px) 720px"></figure><p><strong>Ready to build your Solana staking program on institutional-grade infrastructure?</strong> <a href="http://p2p.org/?ref=p2p.org">P2P.org</a> provides non-custodial, validator-level Solana staking for institutions with full reward attribution and reporting built in. <a href="https://p2p.org/networks/solana?ref=p2p.org">Explore P2P.org Solana Staking</a></p><h2 id="due-diligence-checklist">Due Diligence Checklist</h2><p>For staking product managers, risk committees, and compliance teams evaluating a Solana staking structure.</p><p><strong>Native staking:</strong></p><ul><li>[ ] Custody architecture is non-custodial with client keys and client control</li><li>[ ] Validator selected based on infrastructure quality, incident history, and geographic distribution</li><li>[ ] Epoch lock-up timeline integrated into liquidity management framework</li><li>[ ] Validator-level reward reporting available in accounting-compatible format</li><li>[ ] Validator governance participation policy documented</li><li>[ ] SLA framed around operational practices, not performance guarantees</li></ul><p><strong>Liquid staking (additional layer):</strong></p><ul><li>[ ] Smart contract audit history reviewed and accepted by the risk committee</li><li>[ ] Slashing incident and depeg history reviewed for selected protocol</li><li>[ ] LST accounting treatment confirmed with legal and finance teams</li><li>[ ] Tax treatment of LST rewards confirmed per operating jurisdiction</li><li>[ ] The validator delegation strategy of the protocol is reviewed and acceptable</li><li>[ ] DeFi deployment strategy, if any, has independent risk approval</li></ul><h2 id="key-takeaway">Key Takeaway</h2><p>For institutional participants in Solana's proof-of-stake network, the native vs. liquid staking decision is not primarily about yield optimisation. It is about risk architecture, custody posture, and mandate alignment. Native staking provides the cleanest institutional baseline with full custody control, no smart contract exposure, and a regulatory posture that maps directly to the March 2026 SEC and CFTC interpretation. Liquid staking offers capital efficiency and composability at the cost of additional risk layers that each institution must explicitly evaluate and accept.</p><p>With Alpenglow improving native staking economics, the SEC commodity ruling removing regulatory ambiguity, and the LST market becoming more complex rather than simpler, the case for starting with a rigorous native staking foundation has never been stronger. Build the baseline correctly, then evaluate whether your mandate and risk framework support expanding from there.</p><p><em>Protocol-generated rewards are determined by network conditions and are variable. </em><a href="http://p2p.org/?ref=p2p.org"><em>P2P.org</em></a><em> does not control or set reward rates. Slashing risks are protocol-defined and client-borne. Operational safeguards are implemented to reduce slashing exposure, but do not eliminate protocol-level risk.</em></p><h2 id="faq">FAQ</h2><p><strong>What is the difference between native staking and liquid staking for Solana institutional programs?</strong></p><p>In native staking, SOL is delegated directly from a client-controlled wallet to a validator. The delegator retains full custody at all times, and the staked SOL never leaves their control. In liquid staking, SOL is deposited into a protocol which issues a liquid staking token representing the staked position. The LST can be traded or used in DeFi, but introduces additional risk layers, including smart contract exposure and potential depeg risk that native staking does not carry.</p><p><strong>Is liquid staking on Solana permitted under institutional mandates following the March 2026 ruling?</strong></p><p>As of March 17, 2026, the SEC and CFTC jointly confirmed that liquid staking activities do not constitute securities transactions, provided the provider does not fix or guarantee reward amounts. This ruling removed the primary regulatory barrier that had previously caused many institutional compliance teams to restrict LST exposure. Whether a specific mandate permits LST exposure remains a question for each institution's legal and risk teams.</p><p><strong>How does the Alpenglow upgrade affect Solana staking for institutions?</strong></p><p>Alpenglow eliminates validator voting fees, which had previously represented a meaningful operating cost, reducing net rewards for both validators and delegators. When deployed in 2026, it improves the net reward rate of native staking programs without changing their risk posture. This compresses the yield differential between native and liquid staking, making native staking more competitive for institutions where the additional risk layers of LSTs are not warranted by the mandate.</p><p><strong>What is the unstaking timeline for institutional native SOL staking?</strong></p><p>Native SOL staking has an unstaking period of approximately two epochs, or around four to five days under normal network conditions. This lock-up period is a material liquidity consideration for institutional programs and should be integrated into position sizing and liquidity management frameworks before capital is deployed.</p><p><strong>How should institutions account for liquid staking tokens?</strong></p><p>LSTs are tokens representing staked positions and accrued rewards. Their accounting treatment, particularly for mark-to-market movements, reward recognition, and tax treatment, may differ from native staked SOL depending on jurisdiction and applicable accounting standards. Institutions should obtain specific legal and accounting guidance for their operating jurisdiction before deploying into LST positions.</p><p><strong>What due diligence should institutions conduct on a liquid staking protocol?</strong></p><p>Key areas include the protocol's smart contract audit history and any prior incidents, its slashing and depeg history, its validator delegation strategy and whether it aligns with governance obligations, the accounting and tax treatment of LST rewards in the relevant jurisdiction, and whether the protocol has had independent security reviews by recognised firms.</p><hr><p><strong><em>Disclaimer</em></strong></p><p>This article is provided for informational purposes only and does not constitute legal, regulatory, compliance, or investment advice. Regulatory obligations may vary depending on jurisdiction and specific business activities. Readers should consult their own legal and compliance advisors regarding applicable requirements.</p>
from p2p validator
<hr><h2 id="series-defi-infrastructure-for-institutions">Series: DeFi Infrastructure for Institutions</h2><p>P2P.org's content series for regulated institutions evaluating on-chain capital allocation. Each article addresses a specific infrastructure, governance, or compliance dimension that determines whether a DeFi allocation can clear institutional approval and operate within mandate.</p><p>This article opens the second trilogy in the series, examining the regulatory environment that is accelerating the infrastructure requirement for institutional DeFi allocation. The first trilogy established the structural gap: why DeFi vault architecture was not built for institutional risk tolerance, why the curator incentive structure creates a conflict of interest, and why mandate validation at execution is the governance standard institutions require. This trilogy examines the external pressure making that governance standard a regulatory inevitability rather than an optional upgrade.</p><p><em>Previously in this series: </em><a href="https://p2p.org/economy/mandate-validation-defi-institutional-allocators/"><em>Mandate Validation at Execution: What It Means for Regulated Allocators</em></a></p><h2 id="introduction">Introduction</h2><p>MiCA came into force on December 30, 2024. Its stablecoin provisions had already been applied since June 2024. The Transfer of Funds Regulation, which enforces the Travel Rule across crypto-asset transfers, became enforceable the same day. Seven countries outside the EU are actively drafting MiCA-style regulations. The era of regulatory arbitrage within Europe is over.</p><p>And yet MiCA explicitly excludes fully decentralised DeFi protocols from its scope. Protocols like Aave, Morpho, and Euler, where no identifiable entity manages the primary functions, are not directly regulated by MiCA. The regulation is designed for centralised entities: issuers, exchanges, custodians, and service providers.</p><p>This creates an apparent paradox that institutional allocators and vault operators evaluating DeFi exposure need to understand clearly. MiCA does not regulate the protocols. But it comprehensively regulates the entities that interact with them on behalf of institutional clients. And it introduces governance requirements around conflict of interest management, audit trail production, and role separation that map directly onto the three structural gaps the first trilogy of this series identified.</p><p>The result is not that MiCA makes DeFi allocation impossible. It is that MiCA makes the governance infrastructure required to do DeFi allocation compliant non-negotiable for any regulated entity operating within its scope.</p><figure class="kg-card kg-image-card kg-card-hascaption"><img src="https://p2p.org/economy/content/images/2026/04/-mica-defi-vaults-scope-governance-requirements.jpg" class="kg-image" alt="A two-column diagram showing entities within MiCA scope on the left including CASP operators, custodians, vault operators, and service providers, and entities outside direct MiCA scope on the right including Aave, Morpho, and Euler as fully decentralised protocols, with an indirect pressure arrow pointing left and three governance requirement boxes below covering conflict of interest documentation, audit trail production, and Travel Rule compliance." loading="lazy" width="2000" height="1304" srcset="https://p2p.org/economy/content/images/size/w600/2026/04/-mica-defi-vaults-scope-governance-requirements.jpg 600w, https://p2p.org/economy/content/images/size/w1000/2026/04/-mica-defi-vaults-scope-governance-requirements.jpg 1000w, https://p2p.org/economy/content/images/size/w1600/2026/04/-mica-defi-vaults-scope-governance-requirements.jpg 1600w, https://p2p.org/economy/content/images/2026/04/-mica-defi-vaults-scope-governance-requirements.jpg 2240w" sizes="(min-width: 720px) 720px"><figcaption><i><em class="italic" style="white-space: pre-wrap;">What MiCA regulates directly, what falls outside its scope, and the three governance requirements it introduces for vault operators.</em></i></figcaption></figure><h2 id="learnings-for-busy-readers">Learnings for Busy Readers</h2><p>Short on time? Here are the key takeaways. For the full analysis and supporting data, continue reading below.</p><p>MiCA does not directly regulate DeFi protocols with no identifiable intermediary. What it comprehensively regulates are the operators, custodians, and service providers that interact with those protocols on behalf of EU clients. That indirect effect is the critical development for institutional DeFi allocation.</p><p>For vault operators, MiCA's CASP licensing requirements introduce mandatory governance standards around conflict of interest management, client asset safeguarding, and audit trail production. These requirements apply to any entity providing crypto-asset management services to EU clients, regardless of whether the underlying protocols are themselves regulated.</p><p>For institutional allocators, MiCA's conflict-of-interest framework scrutinises the commingling of curator and operator roles, which the first trilogy identified as a structural problem. MiCA Articles 68 through 73 require documented conflict of interest policies, auditable complaint processes, and controls for outsourcing risk. The curator-as-operator arrangement that characterises most DeFi vaults does not satisfy these requirements without additional governance infrastructure.</p><p>The Travel Rule adds a separate and immediate requirement. Since December 30, 2024, every crypto-asset transfer involving a CASP must be accompanied by full originator and beneficiary data. For DeFi vault transactions, producing that data requires infrastructure that most vault products were not designed to generate.</p><h2 id="what-mica-does-and-does-not-cover">What MiCA Does and Does Not Cover</h2><p>Understanding MiCA's scope precisely is the starting point for any serious analysis of its implications for DeFi vault allocation.</p><p>MiCA regulates crypto-asset service providers: exchanges, custodians, portfolio managers, transfer agents, and advisors operating in or serving clients in the EU. It requires CASP authorisation from a national competent authority, with EU-wide passporting once authorised. As of late 2025, over 50 CASPs had received MiCA authorisation across the European Economic Area, with Germany, the Netherlands, and Luxembourg attracting the largest concentrations of licensed entities.</p><p>MiCA does not regulate fully decentralised protocols. Where no identifiable entity manages the primary functions of a DeFi protocol, MiCA cannot be applied. The regulation acknowledges this explicitly. Protocols like Aave, Morpho, and Euler, where governance is distributed, and no single entity controls execution, are not in scope.</p><p>The boundary, however, is not always clean. MiCA applies a substance-over-form test: where a protocol has identifiable operators managing primary functions, the protocol may fall within scope regardless of how it characterises itself. More than 50% of DeFi protocols still lack clarity on their MiCA classification as of 2025. For vault operators with identifiable governance structures, the risk of falling within MiCA's scope is real and requires legal assessment rather than assumption.</p><p>What is unambiguous is that any entity providing crypto-asset portfolio management services to EU clients is a CASP under MiCA and must be authorised accordingly. A vault operator managing assets on behalf of institutional EU clients is providing a service that falls squarely within MiCA's CASP definition. The protocols the vault operator interacts with may not be regulated. The operator is.</p><h2 id="what-mica-requires-of-vault-operators">What MiCA Requires of Vault Operators</h2><p>For vault operators that fall within MiCA's CASP framework, the governance requirements are specific and operationally demanding.</p><h3 id="conflict-of-interest-management">Conflict of interest management</h3><p>MiCA Articles 68 through 73 require CASPs to maintain documented policies identifying and managing conflicts of interest, auditable complaint processes, and controls for outsourcing risk. The curator-as-operator arrangement that characterises most DeFi vaults creates an immediate conflict of interest disclosure problem. A single entity designing the strategy, executing the rebalances, and managing the operator infrastructure has conflicts at every stage: the curator's TVL incentive, the performance fee structure, and the absence of independent oversight. MiCA does not prohibit these arrangements but requires that they be documented, disclosed, and managed through controls that can be demonstrated to a regulator. A vault operator who cannot produce that documentation has a compliance gap.</p><h3 id="client-asset-safeguarding">Client asset safeguarding</h3><p>MiCA requires strict segregation and safeguarding of client funds, with daily reconciliation and documented controls for preventing misuse. For DeFi vault operators managing institutional assets, this requirement extends to the on-chain environment. The operator must be able to demonstrate, at any point, where client assets are held, in what protocols, at what valuations, and under what controls. A vault product that cannot produce this audit chain does not satisfy MiCA's safeguarding requirement.</p><h3 id="audit-trail-production">Audit trail production</h3><p>MiCA requires CASPs to maintain chronological, automatically recorded audit logs of all trades and instructions, in an easily searchable format. This is the compliance log requirement that the first trilogy identified as absent from most DeFi vault products. Under MiCA, it is not a best practice. It is a legal obligation for any CASP providing vault management services to EU clients.</p><h3 id="dora-operational-resilience">DORA operational resilience</h3><p>The Digital Operational Resilience Act applied from January 17, 2025, to all financial entities regulated under EU law, including MiCA-licensed CASPs. DORA requires documented ICT risk management frameworks, mandatory incident reporting, regular resilience testing, and oversight of third-party ICT providers. For vault operators whose infrastructure depends on third-party oracle providers, bridge infrastructure, or external data feeds, DORA introduces specific oversight obligations for each of those dependencies.</p><blockquote><strong>The institutional digital asset space moves fast.</strong> Our subscribers get structured analysis across staking, DeFi vaults, and regulation through <em>DeFi Dispatch</em>, <em>Institutional Lens</em>, <em>DeFi Infrastructure for Institutions</em>, and<em>Legal Layer</em>. No noise. Just the signals that matter. <strong>Subscribe to the newsletter at the bottom of this page.</strong></blockquote><h2 id="what-mica-requires-of-institutional-allocators">What MiCA Requires of Institutional Allocators</h2><p>For institutional allocators rather than operators, MiCA's implications operate at a different level. The allocator is typically not the CASP. But the allocator's counterparties are, and MiCA changes what those counterparties are required to provide.</p><h3 id="counterparty-due-diligence">Counterparty due diligence</h3><p>An institutional allocator interacting with a DeFi vault through a MiCA-licensed custodian or service provider can rely on that intermediary's CASP authorisation as a baseline governance signal. But authorisation is a threshold, not a guarantee of mandate alignment. The allocator still needs to verify that the specific governance infrastructure of the vault product satisfies its own mandate requirements, including pre-execution controls, compliance log production, and role separation, beyond what MiCA's minimum requirements specify.</p><h3 id="travel-rule-compliance">Travel Rule compliance</h3><p>Since December 30, 2024, every crypto-asset transfer involving a CASP requires full originator and beneficiary data. For institutional allocators using a custodian to interact with DeFi vault protocols, the custodian bears the Travel Rule obligation. But the allocator needs to verify that the custodian's infrastructure can produce compliant transfer data for every vault interaction, including rebalances initiated by the curator. Many vault architectures do not generate the data structure that Travel Rule compliance requires, because the rebalance is initiated by a smart contract rather than a named originator. Identifying and resolving that gap is the allocator's due diligence responsibility.</p><h3 id="conflict-of-interest-framework-alignment">Conflict of interest framework alignment</h3><p>MiCA's conflict of interest requirements apply to the CASP that the allocator uses. But the allocator's own governance framework, particularly for regulated custodians and asset managers subject to MiFID II, AIFMD, or equivalent frameworks, extends those requirements to the underlying vault architecture. If the curator and operator of the vault are the same entity, the allocator's compliance function must be able to demonstrate that the resulting conflict of interest is identified, disclosed, and managed. That demonstration requires the vault to produce documentation that most current products do not generate.</p><h2 id="mica-as-an-architecture-signal-not-just-a-compliance-checklist">MiCA as an Architecture Signal, Not Just a Compliance Checklist</h2><p>The most important implication of MiCA for DeFi vault infrastructure is not the specific compliance requirements it introduces for CASPs. It is the signal those requirements send about where the market is heading.</p><p>MiCA represents the EU's decision to regulate crypto-asset services the same way it regulates traditional financial services. The governance requirements it introduces for vault operators, conflict of interest management, client asset safeguarding, audit trail production, and operational resilience are the same requirements that have applied to traditional delegated asset managers for decades under MiFID II. MiCA is not inventing new governance standards. It is extending existing ones into the on-chain environment.</p><p>Seven countries outside the EU are actively drafting MiCA-style regulations. The IOSCO principles that informed MiCA's design are being referenced in regulatory discussions in the United States, Singapore, and the United Kingdom. The institutional governance standard that MiCA formalises for the EU is becoming the reference standard for regulated institutional participation in on-chain capital markets globally.</p><p>For vault operators and institutional allocators, this means the governance infrastructure question is not a European compliance question. It is a question about where the global market for institutional on-chain capital is heading. The operators who build the governance layer now, with pre-execution controls, exportable compliance logs, and contractual role separation, will be positioned to serve institutional capital as the regulatory environment converges. The operators who treat MiCA compliance as a checkbox exercise will find the governance gap exposed in the next jurisdiction that formalises the same requirements.</p><h2 id="key-takeaway">Key Takeaway</h2><p>MiCA does not regulate DeFi protocols. It regulates the operators and service providers that interact with those protocols on behalf of institutional clients, and it introduces governance requirements that map precisely onto the structural gaps the first trilogy of this series identified.</p><p>For vault operators, MiCA's conflict of interest, safeguarding, and audit trail requirements are not optional for any entity providing vault management services to EU clients. The curator-as-operator arrangement that characterises most DeFi vaults creates documentation and disclosure obligations that require governance infrastructure beyond what most current products provide.</p><p>For institutional allocators, MiCA changes the counterparty due diligence question. The allocator now needs to verify not just that their custodian or service provider is MiCA-authorised, but that the specific vault architecture they are accessing can satisfy MiCA's audit trail, Travel Rule, and conflict of interest requirements in practice.</p><p>The governance infrastructure that satisfies both requirements, pre-execution controls, exportable compliance logs, and contractual role separation, is the same infrastructure that the first trilogy established as the missing layer in DeFi vault architecture. MiCA makes building it a regulatory inevitability for operators serving EU institutional clients. The direction of travel for every other major jurisdiction suggests it will not remain a European requirement for long.</p><p><em>Next in this series: Travel Rule Enforcement and the Onchain Compliance Gap</em></p><h2 id="frequently-asked-questions-faqs">Frequently Asked Questions (FAQs)<br></h2><h3 id="does-mica-regulate-defi-protocols-like-aave-morpho-and-euler">Does MiCA regulate DeFi protocols like Aave, Morpho, and Euler?</h3><p>No, not directly. MiCA applies a substance-over-form test: fully decentralised protocols with no identifiable entity managing primary functions are excluded from its scope. Aave, Morpho, and Euler operate as decentralised protocols and are not directly regulated under MiCA. However, any entity providing crypto-asset portfolio management services using those protocols on behalf of EU clients is a CASP under MiCA and must be authorised accordingly. The protocols are not regulated. The operators using them to serve EU institutional clients are.</p><h3 id="what-is-the-mica-casp-authorisation-requirement-and-who-does-it-apply-to">What is the MiCA CASP authorisation requirement, and who does it apply to?</h3><p>Any entity providing crypto-asset services to EU clients, including portfolio management, custody, exchange, and transfer services, must obtain CASP authorisation from a national competent authority in an EU member state. Authorisation in one member state provides passporting rights across all 27 EU countries. Capital requirements range from €50,000 to €150,000, depending on the service type. As of late 2025, over 50 CASPs had received authorisation, with transitional arrangements for pre-existing providers expiring across member states by July 2026.</p><h3 id="what-does-micas-conflict-of-interest-requirement-mean-for-defi-vault-operators">What does MiCA's conflict of interest requirement mean for DeFi vault operators?</h3><p>MiCA Articles 68 through 73 require CASPs to maintain documented conflict of interest policies, auditable complaint processes, and outsourcing controls. For a vault operator where the curator and operator functions are held by the same entity, MiCA requires that the resulting conflicts be identified, documented, disclosed to clients, and managed through controls that can be demonstrated to a regulator. A vault operator that cannot produce this documentation has a compliance gap under MiCA, regardless of the quality of the underlying strategy.</p><h3 id="what-is-the-travel-rule-and-what-does-it-require-for-defi-vault-transactions">What is the Travel Rule, and what does it require for DeFi vault transactions?</h3><p>The Transfer of Funds Regulation, which implements the Travel Rule for crypto-asset transfers, became enforceable on December 30, 2024. It requires every crypto-asset transfer involving a CASP to be accompanied by full originator and beneficiary data: name, account identifier, address or national ID, and date of birth. For DeFi vault rebalances initiated by smart contracts rather than named originators, producing compliant Travel Rule data requires infrastructure that most vault architectures were not designed to generate. Institutional allocators need to verify that their custodian's infrastructure can produce this data for every vault interaction before initiating transactions.</p><h3 id="how-does-mica-interact-with-dora-for-vault-operators">How does MiCA interact with DORA for vault operators?</h3><p>The Digital Operational Resilience Act applied from January 17, 2025, to all financial entities regulated under EU law, including MiCA-licensed CASPs. DORA requires documented ICT risk management frameworks, mandatory incident reporting to regulators, regular resilience testing, and oversight of third-party ICT providers. For vault operators whose infrastructure depends on external oracle providers, bridge infrastructure, or off-chain data feeds, DORA introduces specific oversight obligations for each dependency. Non-compliance with DORA carries the same enforcement consequences as non-compliance with MiCA, making it a parallel compliance obligation rather than a secondary one.</p><hr><p><a href="http://p2p.org/?ref=p2p.org"><em>P2P.org</em></a><em> builds the protection layer that sits between regulated institutions and DeFi execution environments, independently of the curators who manage allocation strategies. If you are evaluating the infrastructure requirements for a DeFi allocation program, </em><a href="https://p2p.org/?ref=p2p.org#form"><em>talk to our team</em></a><em>.</em></p><hr><p><strong><em>Disclaimer</em></strong></p><p>This article is provided for informational purposes only and does not constitute legal, regulatory, compliance, or investment advice. Regulatory obligations may vary depending on jurisdiction and specific business activities. Readers should consult their own legal and compliance advisors regarding applicable requirements.</p>
from p2p validator