Subscribe to P2P-economy
Stay up to date! Get all the latest & greatest posts delivered straight to your inbox
SubscribeEvery Solana transaction sender promises speed. Few explain where that speed actually comes from.
Solana transaction landing is about speed. But speed is not just how fast a transaction is sent. It depends on how transactions are routed through staked validator paths that give your flow priority bandwidth to the block leader, before competing with everyone else.
The difference is not small. It determines whether a transaction lands or misses entirely.
When a transaction is submitted on Solana, it is sent toward the block leader. But how it gets there determines whether it lands.
Transactions are forwarded by RPC nodes to the current and upcoming leaders via TPU and QUIC. However, routing conditions such as bandwidth, prioritization, and connection quality define the result.
Two transactions submitted at the same time can produce very different outcomes depending on how they are routed.
This is where Solana transaction landing performance is decided.
Public RPC endpoints are designed for accessibility, not execution performance. They introduce structural limitations that affect Solana transaction landing speed.
Public RPC nodes forward transactions to leaders, but through a constrained set of routes. If those paths are congested, transactions arrive later than competing flow.
Traffic from thousands of users competes for the same resources. There is no prioritization for execution-critical transactions.
Public RPC nodes forward transactions through connections without stake backed priority. This limits bandwidth and increases delays during periods of high demand.
For general usage, this is sufficient. For trading, arbitrage, and liquidations, this becomes a limiting factor.
The key idea is simple.
Solana transaction landing speed is determined by routing, not just submission latency. Infrastructure must:
This is a network design problem. Not an API problem.
Solana includes Stake Weighted Quality of Service (SWQoS), a mechanism that prioritizes traffic based on validator stake.
In practice:
SWQoS is a critical factor in Solana transaction landing, especially for execution focused teams. Transactions submitted through unstaked public RPCs compete at a structural disadvantage.
Latency still matters, but not only in geographic terms. Network proximity defines performance:
Even small differences in latency can determine whether a transaction lands in the first slot or misses the opportunity entirely. Learn more about how Solana's validator architecture affects transaction delivery.
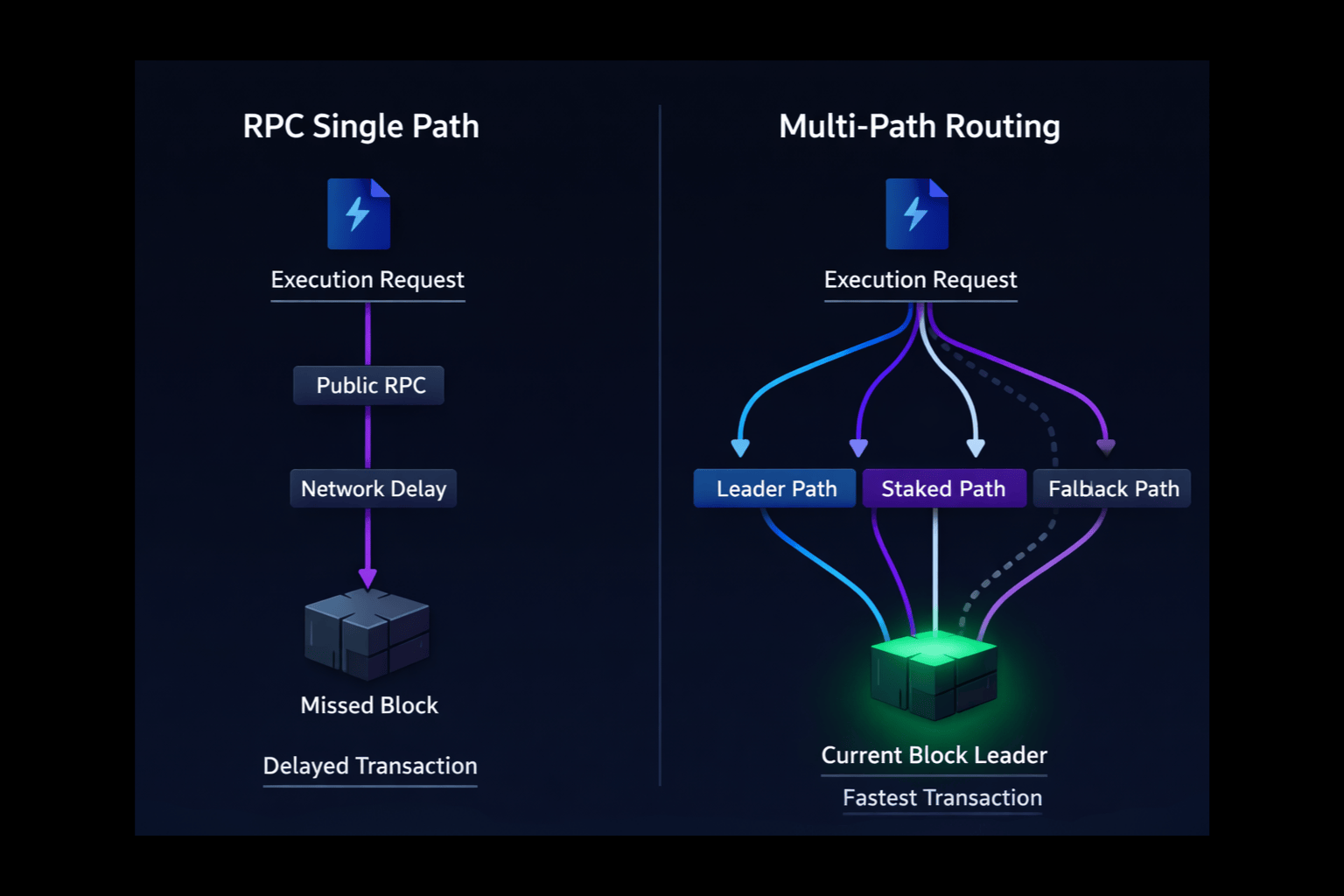
Relying on a single route assumes that the path will succeed. In practice, this is not reliable.
Multi-path routing improves Solana transaction landing by sending transactions through multiple routes simultaneously:
The first successful path determines the outcome. This improves consistency and landing probability, especially during congestion.
Improving Solana transaction landing requires a Solana sender built with the right infrastructure: one that uses Stake Weighted QoS-enabled paths, routes through validator-level connections, minimizes delays and contention, and supports multi-path delivery.
Without this, execution strategies are limited by infrastructure performance. Syncro Sender is a Solana sender built specifically for execution critical workflows, using validator-level routing and multi-path delivery to reach the block leader first.
For a deeper look at how it works, see the Syncro Sender overview.
For execution focused teams, this changes how infrastructure should be evaluated.
Instead of asking: How fast is the endpoint?
The better question is: How are transactions routed, and do they have priority access?
If you are running execution critical workflows on Solana, speed is only part of the equation. The real question is how that speed is achieved.
Test Syncro Sender alongside your current setup and compare Solana transaction landing performance using real transaction flow. You can get started in minutes via the quick start documentation.
On Solana, speed defines execution.
But speed does not come from sending faster.
It comes from routing smarter.
That is what defines Solana transaction landing.
Solana transaction landing refers to whether a submitted transaction successfully reaches the block leader and is included in a block. It is the key metric that determines execution success on Solana.
Solana transactions fail to land when they arrive too late to the block leader or lose priority against competing transactions. This is often caused by congestion, limited routing paths, or insufficient priority bandwidth.
Solana transaction landing speed is affected by routing paths, validator connections, network congestion, and whether the transaction is sent through a Solana sender with Stake Weighted QoS-enabled infrastructure.
Yes. Public RPC infrastructure can limit Solana transaction landing performance due to shared bandwidth, limited routing paths, and a lack of stake-backed priority connections.
Stake-weighted Quality of Service is a mechanism that prioritizes traffic based on validator stake. Transactions routed through staked connections receive higher priority and are more likely to reach the block leader faster.
Routing determines how quickly and reliably a transaction reaches the block leader. Even if two transactions are submitted simultaneously, the one with the better routing will be processed first.
Multi-path routing is the practice of sending a transaction through multiple validator routes simultaneously. This increases the probability that at least one path reaches the leader early.
To improve Solana transaction landing, use a Solana sender that provides validator-level routing, stake-weighted QoS access, optimized network proximity, and multi-path delivery, such as Syncro Sender by P2P.org.
<p><strong>Series:</strong> Institutional Lens | Validation Infrastructure</p><h2 id="summary">Summary</h2><p>Proof-of-stake networks have crossed a threshold. With over 30% of Ethereum's total supply now staked — representing more than $100 billion in economic security — institutional participants are no longer early adopters. They are load-bearing infrastructure. That changes the risk calculus entirely. For digital asset custodians, ETF issuers, treasury teams, and crypto-native funds, participation in validator networks is no longer primarily a question of reward optimization. It is a question of operational governance, risk architecture, and institutional accountability. This piece explains why a validator protection layer — a defined set of operational, technical, and governance safeguards — is no longer optional for institutions operating at scale in proof-of-stake environments.</p><h2 id="if-you-only-have-two-minutes">If You Only Have Two Minutes</h2><p>This article is the first in the <strong>Institutional Lens</strong> series, which unpacks protocol mechanics and infrastructure decisions for institutional participants in proof-of-stake networks.</p><p><strong>Recommended reading:</strong> Before or after this piece, explore our breakdown of how slashing works at the protocol level — a direct companion to the governance and risk architecture discussed here: → <a href="https://p2p.org/economy/ethereum-slashing-explained-what-custodians-funds-exchanges-must-know/">Ethereum Slashing Explained: What Custodians, Funds & Exchanges Must Know</a></p><p><strong>What this piece covers:</strong></p><ul><li>Why institutional scale amplifies validator risk exposure</li><li>What a protection layer actually means operationally</li><li>The governance and capital implications of getting it wrong</li><li>What to look for in a validator infrastructure partner</li></ul><h2 id="who-this-is-for">Who This Is For</h2><p>This article is written for professionals operating at the intersection of institutional finance and blockchain infrastructure. Specifically:</p><ul><li><strong>Digital asset custodians</strong> managing staked positions on behalf of clients</li><li><strong>ETF and ETP issuers</strong> with staking-enabled products or pending approvals</li><li><strong>Crypto-native funds</strong> and treasury teams with direct validator exposure</li><li><strong>Staking product managers</strong> and <strong>validator risk committees</strong> assessing partner infrastructure</li><li><strong>Infrastructure engineers</strong> responsible for validator operations and key security</li></ul><p>If you are deploying, managing, or overseeing significant staked capital in proof-of-stake networks, the risk dynamics described here are directly relevant to your operational posture.</p><h2 id="the-institutional-inflection-point">The Institutional Inflection Point</h2><p>Institutional participation in proof-of-stake networks has moved from exploratory to structural. Between January and June 2025, the amount of staked ETH rose from 34 million to 35.3 million, reaching approximately 29% of the total supply (<a href="https://coinlaw.io/eth-staking-statistics/?ref=p2p.org">CoinLaw</a>). By early 2026, that figure had crossed 30%: a milestone that reflects not just retail participation, but deep institutional commitment.</p><p>Institutional funds currently hold approximately 3.3 million ETH, so around 3% of the circulating supply, through exchange-traded funds alone. With staking ratios already above 27%, ETF staking approvals alone could increase total staked ETH by more than 10% (<a href="https://www.coindesk.com/coindesk-indices/2025/05/07/ether-etfs-and-institutional-staking-what-s-at-stake?ref=p2p.org">CoinDesk</a>).</p><p>This is no longer a niche phenomenon. Banks, asset managers, hedge funds, pension funds, venture capital firms, and centralized exchanges have all entered the sector. Staking solutions designed specifically for professional investors have gained significant momentum, shaping a distinct vertical now known as staking-as-a-service (<a href="https://coinshares.com/us/insights/knowledge/institutional-staking-on-the-rise/?ref=p2p.org">CoinShares</a>).</p><p>The regulatory backdrop has also shifted decisively. In Europe, the MiCA framework provides clear operational and compliance requirements for regulated entities. In the United States, the SEC's August 2025 decision not to classify liquid staking as a security removed one of the main legal obstacles for large allocators. The IRS subsequently issued new guidance providing a clear path for trusts to stake digital assets without jeopardizing their tax status (<a href="https://coinshares.com/us/insights/knowledge/institutional-staking-on-the-rise/?ref=p2p.org">CoinShares</a>)</p><p>All of these points to the same structural reality: institutional capital is now deeply embedded in proof-of-stake infrastructure. And with that comes a risk exposure that did not exist at scale before.</p><h2 id="what-risk-actually-looks-like-at-institutional-scale">What Risk Actually Looks Like at Institutional Scale</h2><p>The risks of validator participation are protocol-defined and well-understood. What changes at institutional scale is the magnitude of consequence.</p><h3 id="slashing-rare-but-asymmetric">Slashing: Rare, But Asymmetric</h3><p>Slashing is the protocol-level penalty applied when a validator behaves in ways that threaten network integrity, primarily double-signing or prolonged inactivity. Historical data shows that only 0.03% of all Ethereum validators have ever been slashed since staking launched in December 2020. Of those, the largest realized loss was approximately 3% of staked capital (<a href="https://www.ishares.com/us/insights/portfolio-insights/cryptocurrency-staking-guide-ethereum?ref=p2p.org">iShares</a>).</p><p>Low frequency does not mean low consequence. In September 2025, 39 validators were slashed in one of the largest correlated slashing events since Ethereum's transition to proof-of-stake. The incident was traced to operator-side infrastructure issues involving third-party staking providers (<a href="https://www.coindesk.com/tech/2025/09/10/ethereum-rare-mass-slashing-event-linked-to-operator-issues?ref=p2p.org">CoinDesk</a>). What began as an operational failure at the infrastructure layer resulted in compounded penalties — because when multiple validators are slashed simultaneously, Ethereum's protocol enforces additional inactivity leaks that amplify the financial impact.</p><p>For a deeper breakdown of how slashing mechanics work at the protocol level, see: <a href="https://p2p.org/economy/ethereum-slashing-explained-what-custodians-funds-exchanges-must-know/">Ethereum Slashing Explained: What Custodians, Funds & Exchanges Must Know</a></p><p>For an institution managing hundreds of millions in staked capital, a correlated slashing event is not a theoretical scenario. It is a risk that must be engineered around.</p><h3 id="operational-and-key-security-risk">Operational and Key Security Risk</h3><p>Institutions that run their own validators or manage staking operations in-house may face challenges in securely managing private keys, validator operations, rewards tracking, and protocol upgrades. These processes require specialized infrastructure and consistent operational uptime, introducing technical complexity and potential security vulnerabilities if operators lack deep experience (<a href="https://www.coinbase.com/institutional/research-insights/resources/education/staking-essentials-institutions?ref=p2p.org">Coinbase</a>).</p><p>Validator key compromise, while rare, carries consequences that extend well beyond the immediate staking position. A compromised key is an operational incident, a governance incident, and potentially a regulatory disclosure event, all at once.</p><h3 id="liquidity-and-lock-up-risk">Liquidity and Lock-Up Risk</h3><p>Staked ETH is less liquid than unstaked capital. Withdrawal timelines are variable depending on network conditions, particularly the number of validators attempting to exit simultaneously. Under normal conditions, withdrawals take several days. During periods of elevated activity, delays can extend to weeks or longer (<a href="https://www.ishares.com/us/insights/portfolio-insights/cryptocurrency-staking-guide-ethereum?ref=p2p.org">iShares</a>).</p><p>For treasury teams and ETF issuers managing redemption obligations alongside staked positions, liquidity risk is not abstract. It is a balance sheet constraint.</p><h2 id="what-a-protection-layer-actually-means">What a Protection Layer Actually Means</h2><p>The term "protection layer" is deliberately structural. It describes a set of architectural, operational, and governance decisions that sit between an institution's capital and the protocol-level risks described above. It is not a product. It is a design posture.</p><figure class="kg-card kg-image-card kg-card-hascaption"><img src="https://p2p.org/economy/content/images/2026/03/P2P-Blog.png" class="kg-image" alt="Diagram showing the four layers of a validator protection layer stack: governance and accountability, reporting and auditability, slashing risk controls, and infrastructure architecture — sitting between institutional capital and protocol-defined risk." loading="lazy" width="2000" height="1304" srcset="https://p2p.org/economy/content/images/size/w600/2026/03/P2P-Blog.png 600w, https://p2p.org/economy/content/images/size/w1000/2026/03/P2P-Blog.png 1000w, https://p2p.org/economy/content/images/size/w1600/2026/03/P2P-Blog.png 1600w, https://p2p.org/economy/content/images/2026/03/P2P-Blog.png 2240w" sizes="(min-width: 720px) 720px"><figcaption><span style="white-space: pre-wrap;">Diagram showing the four layers of a validator protection layer stack: governance and accountability, reporting and auditability, slashing risk controls, and infrastructure architecture, sitting between institutional capital and protocol-defined risk.</span></figcaption></figure><p>A meaningful protection layer has four components:</p><h3 id="1-infrastructure-architecture">1. Infrastructure Architecture</h3><p>The foundation of any protection layer is how the validator infrastructure is built. Institutions should only partner with providers that maintain validators across multiple regions, operating in independent data centers with geographic diversity, multiple client implementations, and dedicated fallback systems (<a href="https://aetsoft.net/blog/institutional-crypto-staking/?ref=p2p.org">Aetsoft</a>). Single points of failure at the infrastructure layer are unacceptable at institutional scale.</p><p>Distributed validator technology (DVT) is increasingly relevant here. By splitting validator key operations across multiple independent operators, DVT reduces the risk of any single infrastructure failure triggering a slashing event — and reduces key compromise risk structurally, not just procedurally. <a href="http://p2p.org/?ref=p2p.org">P2P.org</a>'s <a href="https://p2p.org/products/dvt-staking?ref=p2p.org">DVT staking infrastructure</a> is built specifically around this architecture for institutional participants.</p><h3 id="2-slashing-risk-mitigation-protocols">2. Slashing Risk Mitigation Protocols</h3><p>Anti-slashing measures must be built into the validator operation itself, not bolted on afterward. This means enforced key signing controls that prevent double-signing under any operational circumstance, automated failover logic that prioritizes safety over liveness, and real-time monitoring of validator status with immediate alerting.</p><p>Providers should offer real-time dashboards, alerting tools, and analytics that track validator performance, slashing events, network participation, and reward flow (<a href="https://aetsoft.net/blog/institutional-crypto-staking/?ref=p2p.org">Aetsoft</a>). Observability is not optional. It is the operational nervous system of a well-governed staking program.</p><h3 id="3-governance-and-accountability-structures">3. Governance and Accountability Structures</h3><p>For institutions, governance means documented decision rights, audit trails, and clear accountability for validator operations. Who has the authority to initiate an exit? What is the incident response procedure for a slashing event? How are protocol upgrades evaluated and applied?</p><p>As institutional capital flows into proof-of-stake networks, concerns about operational governance highlight the importance of resilient infrastructure, transparent risk controls, and adherence to high compliance standards across staking providers (<a href="https://coinshares.com/us/insights/knowledge/institutional-staking-on-the-rise/?ref=p2p.org">CoinShares</a>). These are not preferences; they are due diligence requirements that institutional risk committees and investor disclosure obligations demand.</p><h3 id="4-reporting-and-auditability">4. Reporting and Auditability</h3><p>Institutional staking programs require reward attribution at the protocol level, disaggregated by validator and by period, in formats compatible with internal risk systems and external audit requirements. This is not a feature. It is an operational necessity for any entity subject to financial reporting obligations.</p><p><a href="http://p2p.org/?ref=p2p.org">P2P.org</a>'s <a href="https://p2p.org/networks/ethereum?ref=p2p.org">Ethereum staking infrastructure</a> is designed with these institutional reporting requirements as a baseline, not an add-on.</p><h2 id="the-capital-governance-dimension">The Capital Governance Dimension</h2><p>Beyond operational risk, there is a deeper question that institutional participants in proof-of-stake networks often underestimate: governance rights.</p><p>Staking is not passive. In many proof-of-stake protocols, validators and delegators participate in governance decisions — protocol upgrades, parameter changes, treasury allocations. At the scale of institutional participation now entering these networks, staking infrastructure decisions are governance decisions.</p><p>Staking enables institutions to actively participate in the networks they hold, contributing to consensus and security. In many proof-of-stake protocols, stakers gain governance rights, enabling them to vote on protocol upgrades, policy changes, and treasury allocations. This influence can be strategically valuable, allowing institutions to help shape network direction (<a href="https://www.coinbase.com/institutional/research-insights/resources/education/staking-essentials-institutions?ref=p2p.org">Coinbase</a>).</p><p>For institutional participants with fiduciary obligations like ETF issuers, custodians, fund managers, this creates a new category of governance responsibility. The validator infrastructure partner an institution selects is not just an operational vendor. It is a governance representative.</p><h2 id="validator-partner-evaluation-what-institutions-should-be-asking">Validator Partner Evaluation: What Institutions Should Be Asking</h2><p>Selecting a validator infrastructure partner is a risk management decision. The relevant questions are not primarily commercial. They are operational and architectural.</p><p>Key areas of evaluation:</p><ul><li><strong>Infrastructure design:</strong> Is the validator infrastructure geographically distributed? Are multiple client implementations supported? What are the failover protocols?</li><li><strong>Slashing risk controls:</strong> What technical controls prevent double-signing? How are signing key operations secured and access-controlled?</li><li><strong>Incident history:</strong> Has the operator experienced slashing events? What was the root cause, and what architectural changes followed?</li><li><strong>DVT adoption:</strong> Does the operator support or plan to support distributed validator technology for key distribution?</li><li><strong>Reporting capabilities:</strong> Can the operator provide reward-attribution data at the validator level, in formats compatible with institutional reporting requirements?</li><li><strong>Protocol alignment:</strong> How does the operator evaluate and respond to protocol upgrades? Is there a documented governance participation policy?</li></ul><h2 id="due-diligence-checklist">Due Diligence Checklist</h2><p>For validator risk committees, compliance teams, and digital asset managers assessing staking infrastructure partners:</p><ul><li>[ ] Validator infrastructure is geographically distributed across independent data centers</li><li>[ ] Multiple consensus client implementations are supported (client diversity)</li><li>[ ] Anti-double-signing controls are enforced at the key management level</li><li>[ ] Automated failover logic prioritizes safety over liveness</li><li>[ ] Real-time monitoring and alerting for validator performance and anomalies</li><li>[ ] Documented incident response procedure for slashing events</li><li>[ ] Audit trail for all validator key operations and access events</li><li>[ ] Reward reporting at validator level, compatible with institutional accounting requirements</li><li>[ ] Documented governance participation policy for protocol upgrades</li><li>[ ] SLA is framed around operational practices, not performance guarantees, so in line with protocol-defined outcomes</li><li>[ ] No custody of client assets (non-custodial architecture confirmed)</li></ul><h2 id="faq">FAQ</h2><h3 id="what-is-a-validator-protection-layer"><strong>What is a validator protection layer?</strong> </h3><p>A validator protection layer refers to the combination of infrastructure architecture, operational controls, and governance frameworks that an institution or its validator infrastructure partner deploys to manage the protocol-defined risks of staking participation. It is not a product but a design posture that encompasses distributed infrastructure, anti-slashing controls, key security, incident response protocols, and institutional-grade reporting.</p><h3 id="how-often-does-slashing-actually-occur-on-ethereum"><strong>How often does slashing actually occur on Ethereum?</strong> </h3><p>Slashing on Ethereum is rare. Historical data indicates that fewer than 0.03% of all validators have been slashed since the Beacon Chain launched in December 2020. However, correlated slashing events where multiple validators are penalized simultaneously carry amplified penalties due to Ethereum's inactivity leak mechanism. For institutions managing large staked positions, the tail risk of a correlated event is the relevant risk to engineer around, not the average frequency.</p><h3 id="are-slashing-risks-eliminated-by-using-a-third-party-validator-provider"><strong>Are slashing risks eliminated by using a third-party validator provider?</strong></h3><p>No. Slashing risks are protocol-defined and client-borne. A validator infrastructure provider can implement robust controls that reduce the likelihood of slashing events through anti-double-signing logic, distributed key management, and high-availability infrastructure, but cannot eliminate protocol-level risk. Institutions should evaluate the quality of a provider's risk controls rather than expecting guarantees.</p><h3 id="what-is-the-difference-between-operational-risk-and-slashing-risk-in-staking"><strong>What is the difference between operational risk and slashing risk in staking?</strong> </h3><p>Slashing is a specific protocol penalty triggered by defined validator misbehaviors, primarily double-signing. Operational risk is broader. It encompasses validator downtime, key management failures, infrastructure outages, and human errors that may result in missed rewards, delayed withdrawals, or, in severe cases, conditions that trigger slashing. A protection layer addresses both categories.</p><h3 id="how-does-validator-infrastructure-selection-affect-governance-participation"><strong>How does validator infrastructure selection affect governance participation?</strong> </h3><p>In many proof-of-stake protocols, validators participate in governance decisions including protocol upgrades and parameter changes. Institutions delegating to a validator provider are, in effect, delegating governance participation. This creates a fiduciary dimension to infrastructure selection that risk committees and compliance teams should account for explicitly.</p><h3 id="what-should-institutions-look-for-in-staking-reporting-capabilities"><strong>What should institutions look for in staking reporting capabilities?</strong> </h3><p>Institutional staking programs require reward attribution at the protocol level, disaggregated by validator and period, in formats compatible with internal risk management systems and external audit requirements. Providers should be able to demonstrate reporting capabilities before onboarding, not describe them as a future roadmap item.</p><h2 id="key-takeaway">Key Takeaway</h2><p>For digital asset custodians, ETF issuers, treasury teams, and crypto-native funds operating in proof-of-stake networks, the validator infrastructure decision is no longer an operational afterthought. It is a risk management and governance decision with direct capital implications. A protection layer built from distributed infrastructure, enforced anti-slashing controls, non-custodial architecture, and institutional-grade reporting is the baseline expectation for any entity with fiduciary obligations and material staked positions. The question is not whether to implement one. It is whether your current infrastructure partner is actually providing one.</p><p><em>Protocol-generated rewards are determined by network conditions and are variable. P2P does not control or set reward rates. Slashing risks are protocol-defined and client-borne.</em></p><hr><p><strong><em>Disclaimer</em></strong></p><p>This article is provided for informational purposes only and does not constitute legal, regulatory, compliance, or investment advice. Regulatory obligations may vary depending on jurisdiction and specific business activities. Readers should consult their own legal and compliance advisors regarding applicable requirements.</p>
from p2p validator
<p>The past two weeks have brought several developments across DeFi markets, staking infrastructure, and crypto financial products.</p><p>From stablecoin narratives evolving in public discourse to ETF structures integrating staking mechanics, the latest <strong>DeFi news</strong> continues to show how blockchain infrastructure is becoming increasingly embedded into broader financial systems.</p><p>This edition highlights five developments shaping how capital interacts with decentralized networks.</p><p>👉 <strong>Subscribe (at the bottom of the page) to receive DeFi Dispatch</strong> and stay updated on the latest DeFi news and market signals.</p><h2 id="quick-learning-for-busy-readers"><strong>Quick Learning for Busy Readers</strong></h2><ul><li>Stablecoins continue emerging as core infrastructure for global crypto liquidity</li><li>Staking is increasingly being discussed in the context of financial products</li><li>ETF structures are evolving to integrate blockchain-native mechanics</li><li>Tokenized assets remain one of the fastest-growing DeFi segments</li><li>Validator infrastructure continues supporting expanding network participation</li></ul><h2 id="missed-the-previous-defi-dispatch"><strong>Missed the previous DeFi Dispatch?</strong></h2><p>Catch up on the latest DeFi news and signals from the previous edition:</p><p>👉 <a href="https://p2p.org/economy/defi-dispatch-news-and-signals-march-2026-1/">https://p2p.org/economy/defi-dispatch-news-and-signals-march-2026-1/</a></p><h2 id="what%E2%80%99s-driving-defi-markets-this-week"><strong>What’s driving DeFi markets this week?</strong></h2><p><br>The latest DeFi news from the past two weeks reflects a clear trend: infrastructure and capital flows are becoming increasingly interconnected across staking, liquidity, and tokenized financial products.</p><p>From stablecoins reinforcing their role as liquidity rails to new financial products integrating staking mechanics, these developments highlight how DeFi markets continue evolving beyond isolated use cases.</p><p>Below, we break down five key developments and why they matter for participants across crypto markets.</p><h3 id="1-stablecoins-are-becoming-a-core-crypto-resource"><strong>1. Stablecoins Are Becoming a Core Crypto Resource</strong></h3><p><a href="http://p2p.org/?ref=p2p.org">P2P.org</a>’s VP of Institutions, Artemiy Parshakov, recently shared insights on the evolving role of stablecoins, highlighting how they are increasingly functioning as a foundational resource across crypto markets.</p><p>The discussion emphasizes how stablecoins are no longer just a trading tool but a key infrastructure layer enabling liquidity, settlement, and capital movement across decentralized systems.</p><p><strong>Source:</strong> Cointelegraph</p><p><strong>Why is this important?</strong></p><p>Stablecoins underpin a large portion of DeFi activity, acting as:</p><ul><li>settlement layers</li><li>liquidity bases</li><li>collateral assets</li></ul><p>As stablecoins grow, they reinforce the importance of reliable blockchain infrastructure and validator participation to support transaction execution and settlement.</p><h3 id="2-blackrock-advances-ethereum-etf-with-staking-component"><strong>2. BlackRock Advances Ethereum ETF With Staking Component</strong></h3><p>BlackRock continues advancing its Ethereum ETF structure, which may include staking participation for a portion of the fund’s holdings.</p><p>This reflects a broader trend in which traditional financial products are incorporating blockchain-native mechanics, such as staking.</p><p><strong>Source:</strong> Reuters</p><p><strong>Why is this important?</strong></p><p>This development highlights how:</p><ul><li>staking is entering regulated financial structures</li><li>blockchain infrastructure is intersecting with traditional markets</li><li>validator participation becomes indirectly linked to financial products</li></ul><p>It also raises questions around how staking will be treated within regulatory frameworks.</p><h3 id="3-ethereum-staking-participation-remains-strong"><strong>3. Ethereum Staking Participation Remains Strong</strong></h3><p>Recent on-chain data shows continued growth in Ethereum staking participation, with increasing amounts of ETH being committed to validator infrastructure.</p><p>This reflects ongoing confidence in proof-of-stake mechanics and long-term network participation.</p><p><strong>Source:</strong> Glassnode - Ethereum staking metrics</p><p><strong>Why is this important?</strong></p><p>Growing staking participation:</p><ul><li>strengthens network security</li><li>increases reliance on validator infrastructure</li><li>reflects long-term capital allocation within crypto markets</li></ul><p>Validator performance and reliability remain critical as participation scales.</p><h3 id="4-tokenized-assets-continue-expanding-across-defi"><strong>4. Tokenized Assets Continue Expanding Across DeFi</strong></h3><p>Tokenized real-world assets continue gaining traction, with more protocols exploring tokenized treasuries, credit instruments, and on-chain financial products.</p><p>This trend is attracting attention from asset managers and crypto-native funds.</p><p><strong>Source:</strong> CoinShares – Digital asset research report</p><p><strong>Why is this important?</strong></p><p>Tokenization introduces:</p><ul><li>programmable financial assets</li><li>new forms of on-chain liquidity</li><li>integration between traditional and decentralized finance</li></ul><p>As adoption grows, the reliability of underlying blockchain infrastructure becomes increasingly important.</p><h3 id="5-stablecoin-supply-growth-reinforces-defi-liquidity"><strong>5. Stablecoin Supply Growth Reinforces DeFi Liquidity</strong></h3><p>Stablecoin supply continues expanding across major blockchain ecosystems, reinforcing their role as the primary liquidity layer within DeFi.</p><p>Stablecoins remain central to trading, lending, and cross-protocol interactions.</p><p><strong>Source:</strong> CoinMetrics – Stablecoin supply data</p><h3 id="why-is-this-important">Why is this important?</h3><p>Stablecoin growth:</p><ul><li>increases liquidity across DeFi markets</li><li>enables capital movement between protocols</li><li>supports broader ecosystem activity</li></ul><p>This reinforces the importance of scalable and reliable blockchain networks.</p><h2 id="frequently-asked-questions"><strong>Frequently Asked Questions</strong></h2><h3 id="why-is-defi-news-relevant-for-staking-participants"><br><strong>Why is DeFi news relevant for staking participants?</strong></h3><p>DeFi news provides signals about how capital flows through blockchain ecosystems. These flows influence staking participation, network activity, and validator demand.</p><h3 id="are-staking-rewards-fixed"><strong>Are staking rewards fixed?</strong></h3><p>No. Rewards are determined by the underlying protocol and network conditions. They vary depending on validator participation and are not guaranteed.</p><h3 id="why-are-stablecoins-so-important-in-defi"><strong>Why are stablecoins so important in DeFi?</strong></h3><p>Stablecoins act as the primary settlement layer across DeFi. They enable liquidity, trading, and lending without requiring exposure to volatile crypto assets.</p><h3 id="how-does-tokenization-impact-defi-markets"><strong>How does tokenization impact DeFi markets?</strong></h3><p>Tokenization allows traditional assets to be represented on-chain, enabling programmable settlement and integration with DeFi protocols.</p><h2 id="key-takeaways-for-crypto-investors-funds-custodians-exchanges-and-staking-teams"><strong>Key Takeaways for Crypto Investors, Funds, Custodians, Exchanges, and Staking Teams</strong></h2><p>The latest DeFi news highlights several important trends:</p><ul><li>stablecoins continue strengthening their role as DeFi infrastructure</li><li>staking is increasingly integrated into financial products</li><li>validator infrastructure remains central to network operations</li><li>tokenized assets are expanding rapidly</li><li>DeFi markets continue evolving toward broader financial integration</li></ul><p>These developments reinforce how decentralized finance is maturing as an infrastructure layer supporting digital asset markets.</p><p>👉 <strong>Subscribe to DeFi Dispatch and Legal Layer</strong> to stay updated on the latest DeFi news, staking developments, and market signals.</p>
from p2p validator