Subscribe to P2P-economy
Stay up to date! Get all the latest & greatest posts delivered straight to your inbox
SubscribeSeries: DeFi Infrastructure for Institutions
P2P.org's content series for regulated institutions evaluating on-chain capital allocation. Each article addresses a specific infrastructure, governance, or compliance dimension that determines whether a DeFi allocation can clear institutional approval and operate within mandate.
This is part three and the closing article of the opening trilogy on the structural gap between DeFi vault architecture and institutional requirements. Part one established why most DeFi vaults were not built for institutional risk tolerance. Part two examined the conflict of interest at the heart of vault design. This article explains what mandate validation at execution actually means, why it is the standard that regulated institutions apply to every other asset class, and what its absence in DeFi vault architecture costs.
The two preceding articles in this trilogy identified two structural problems in DeFi vault architecture. The first is that the governance assumptions built into most vault products were designed for retail capital and do not accommodate the pre-execution controls, audit trails, or role separation that regulated institutions require. The second is that the curator incentive structure, driven by TVL growth and performance fees rather than mandate alignment, creates a principal-agent conflict with no independent mechanism to detect or resolve it.
Both problems point to the same missing layer: an independent function that validates every allocation decision against the institution's documented mandate parameters before it settles on-chain.
That function has a name in traditional finance. It is called investment compliance monitoring, or mandate validation. It has been the standard infrastructure for regulated delegated asset management for more than two decades. Investment managers, asset owners, and insurers across approximately 30 countries rely on Charles River alone to manage $59 trillion in assets through systems that embed mandate validation directly into order management workflows. That figure represents a single platform. The broader universe of dedicated investment compliance systems, including BlackRock Aladdin and SimCorp, operates at a comparable scale across the global asset management industry. The governance standard that makes institutional delegated mandate management viable in traditional finance is pre-execution validation, not post-execution monitoring. And it is almost entirely absent from DeFi vault architecture today.
This article explains what mandate validation at execution means in practice, why it is the governance standard regulated institutions apply to every other asset class, and what its specific absence in DeFi vault infrastructure means for risk committees, compliance functions, legal teams, investment committees, and the internal champions trying to get allocations approved.
Short on time? Here are the key takeaways. For the full analysis and supporting data, continue reading below.
In traditional delegated asset management, mandate validation is the function that sits between an investment decision and its execution. Before a trade is placed, internal systems verify that the proposed action falls within the documented mandate limits. The check happens before the order reaches the execution desk. If the proposed trade would breach a concentration limit, exceed a leverage threshold, or interact with a restricted counterparty or asset class, it is blocked before it executes. The execution does not proceed until the validation passes.
This is investment compliance monitoring: the function that aligns every execution decision with the regulatory, client, contractual, and risk-based restrictions governing the mandate. The Investment Compliance function is considered one of the most important risk management functions for an asset management firm, precisely because it operates on a pre-trade basis rather than a post-trade basis. Catching a breach after execution means the breach is already in the portfolio. Catching it before execution means it never happens (Source: Stratafs, Investment Compliance: The Missing Link, October 2025.).
The mechanics are well established. Systems like BlackRock Aladdin, Charles River, and SimCorp embed mandate validation directly into order management workflows, automatically checking every proposed trade against coded investment restrictions before placement. The restrictions are documented in the Investment Management Agreement, translated into coded rules, and applied at every execution point. The compliance log records every check run, every breach blocked, and every decision made. That log is the evidence an auditor or regulator requires to verify that capital was managed within mandate parameters at the time each decision was made.
The standard is not post-trade monitoring. Post-trade monitoring tells you what happened. Mandate validation at execution determines what is allowed to happen. These are different functions serving different governance purposes.
Applying mandate validation to DeFi vault allocation requires translating the same governance function into the on-chain execution environment. The principles are identical to traditional finance. The implementation is different because the execution environment is different.
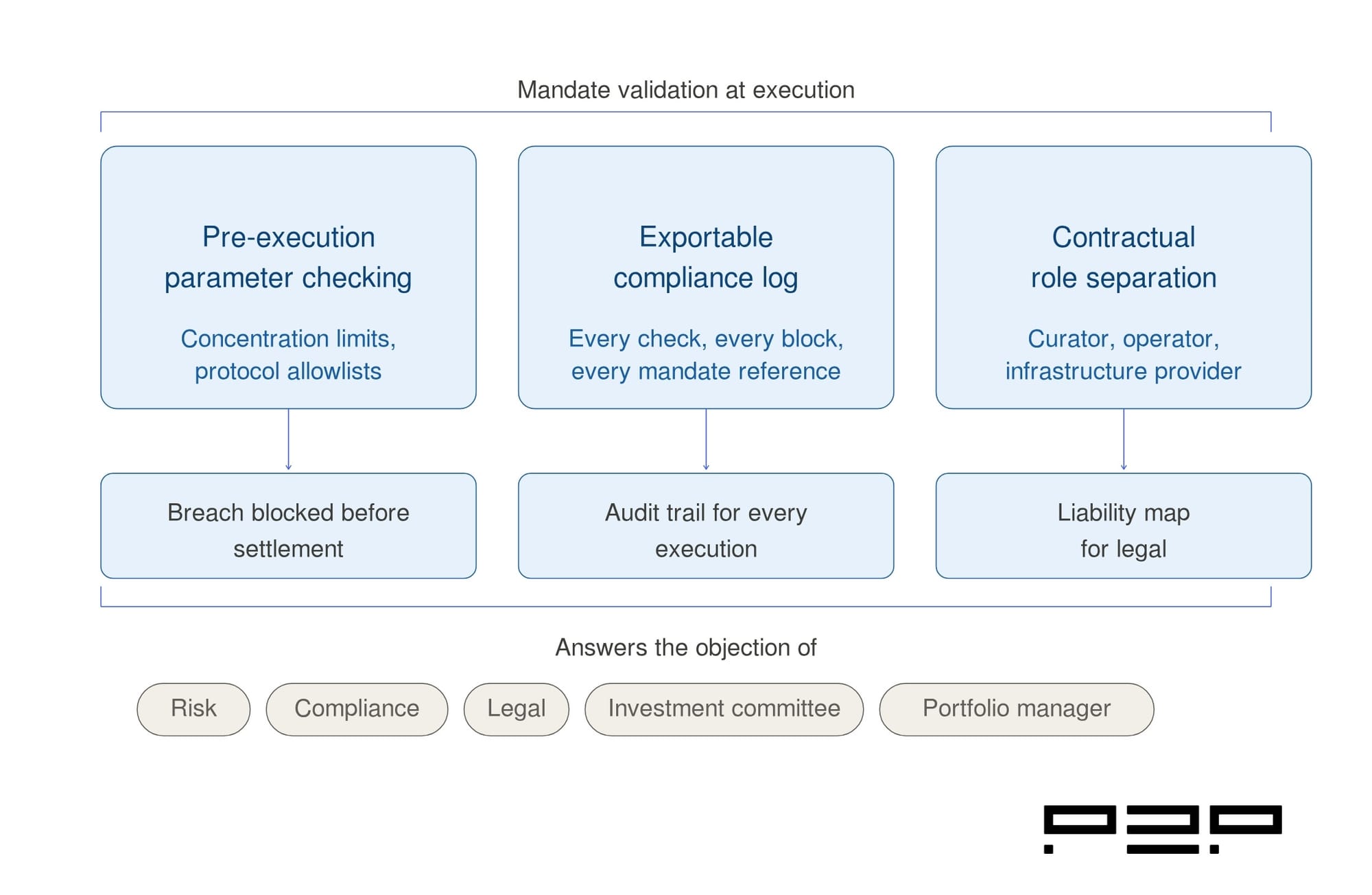
In a DeFi vault context, mandate validation at execution means the following infrastructure exists and operates independently of the curator:
Pre-execution parameter checking. Before any curator rebalance settles on-chain, every transaction is checked against the institution's documented mandate parameters. Concentration limits determine what share of the portfolio can be allocated to any single protocol, asset class, or collateral type. Protocol allowlists specify which protocols the institution has approved for interaction. Slippage thresholds define the maximum acceptable deviation between the expected and executed price. Oracle integrity checks verify that price feeds used for collateral valuations are from approved and reliable sources. A transaction that would breach any of these parameters is blocked before it reaches the settlement layer.
An exportable compliance log. Every check run generates a log entry: the transaction proposed, the parameters checked, the outcome (approved or blocked), and the specific mandate limit referenced for any block. The log is timestamped, sequential, and exportable in a format that an external auditor can verify independently. This is the difference between a dashboard (which shows the current state) and a compliance log (which demonstrates mandate adherence at every historical execution point). Regulators and auditors are not checking the current portfolio. They are checking whether the institution can prove that every past decision was within mandate at the time it was made.
Contractual role separation. Mandate validation functions independently of the curator. The party running the validation layer has no allocation discretion and no protocol referral incentive. Its function is governance: checking every execution against the mandate, blocking what falls outside it, and logging everything. This separation is what allows legal to map the arrangement onto existing frameworks for delegated mandate management. When the curator, the operator, and the validation infrastructure are contractually distinct with non-overlapping liability boundaries, the liability question has a clean answer.
The absence of mandate validation does not produce a single point of failure in the institutional approval process. It produces a failure at every stakeholder stage simultaneously.
The risk committee's objection is pre-execution control. Without it, a concentration limit breach settles on-chain before the risk committee is notified. The committee's job is to ensure capital is managed within the mandate at every execution point. A system that tells them about breaches after they have settled does not satisfy that requirement. It does not matter how good the curator's track record is. A post-execution monitoring tool is not a risk control. It is an incident reporting tool.
The compliance function's objection is the audit trail. A vault dashboard shows position history. A compliance log shows mandate validation history. Those are different things. Compliance needs to demonstrate, not to themselves but to an external auditor, that every execution decision was checked against the documented mandate restrictions at the time it was made. Without a log that records each check, each block, and each mandate reference, that demonstration is not possible.
The legal function's objection is role separation. If the curator who designs the strategy and the operator who manages the infrastructure are the same entity, or if their liability boundaries are undefined, legal cannot map the arrangement onto the frameworks they use for every other delegated mandate relationship. The liability question, who is responsible when something goes wrong, has no clean answer. That is not a question a lawyer can leave open.
The investment committee's objection is defensibility. The committee needs to be able to demonstrate, after the fact, that the allocation was managed within mandate parameters at every point. The compliance log is the evidence that makes that demonstration possible. Without it, the investment committee is approving an allocation it cannot defend to its own clients, regulators, or auditors.
The portfolio manager or internal champion's problem is that none of these objections can be answered with reassurance about the curator's capabilities or the protocol's audit history. Each objection requires a structural answer: a governance mechanism that exists and functions independently of the parties whose decisions it governs. Mandate validation at execution is that structural answer.
This trilogy opened with a question: why does institutional DeFi deployment lag so far behind institutional intent? The EY-Parthenon and Coinbase survey found 83% of institutions plan to increase crypto allocations. Only 24% engage with DeFi. Nomura's 2026 survey of institutions managing over $600 billion in AUM found that nearly 80% plan to allocate to digital assets, with over two-thirds specifically targeting DeFi mechanisms.
The three articles have traced the answer to a single architectural gap.
Part one established that DeFi vault products were built for retail capital. The governance assumptions embedded in that architecture do not accommodate the pre-execution controls, audit infrastructure, or role separation that regulated institutions require as standard.
Part two established that the curator incentive structure creates a structural conflict of interest with no independent mechanism to detect or resolve it. Curators are optimised for TVL and performance fees, not mandate alignment. The architecture provides no independent check between their decisions and on-chain settlement.
Part three establishes that the governance function that would close both gaps, mandate validation at execution, is well-understood, has been standard infrastructure in regulated asset management for over two decades, and is almost entirely absent from DeFi vault architecture today.
The gap is not technical complexity. The systems that run pre-trade compliance checks in traditional finance have been operating reliably at an institutional scale for decades. The gap is architectural: DeFi vault infrastructure was not designed to include this layer because the retail capital it was built for does not require it. Institutional capital does. And the infrastructure layer that provides it is the condition for the capital to follow.
Mandate validation at execution is not a new governance concept. It is the standard that regulated institutions apply to every delegated capital management arrangement, in every asset class, across every jurisdiction. The reason it matters for DeFi is not that DeFi is uniquely risky. It is that DeFi vault architecture, as it exists today, has not yet built the layer that every other institutional-grade asset management product already has.
The three structural gaps this trilogy has identified, the absence of pre-execution controls, the absence of an exportable compliance log, and the absence of contractual role separation between curator, operator, and infrastructure provider, are not separate problems. They are three dimensions of the same missing governance layer.
When that layer exists and functions independently of the curator, the risk committee's objection is answered structurally. The compliance function can produce its audit trail. Legal can map the liability framework. The investment committee can defend the allocation. The internal champion can clear the approval process.
The institutional DeFi deployment gap is not a question of appetite. The appetite is documented and growing. It is a question of infrastructure. And the infrastructure that closes the gap is being built now.
The DeFi Infrastructure for Institutions series continues. The next sequence examines specific dimensions of how the protection layer operates in practice.
Mandate validation at execution is the infrastructure function that checks every allocation decision against a client's documented mandate parameters before it settles on-chain. It is the on-chain equivalent of pre-trade compliance monitoring in traditional asset management: a layer that operates independently of the curator, validates every transaction before it reaches the settlement layer, blocks transactions that would breach mandate parameters, and generates a compliance log that records every check and every block. The key distinction from post-execution monitoring is that validation determines what is allowed to happen before it happens. Monitoring tells you what happened after it did.
Because regulated institutions are required to demonstrate that capital was managed within mandate parameters at every execution point, not that it was managed within mandate parameters most of the time. A system that detects breaches after they settle means breaches are already in the portfolio by the time the risk committee is notified. That sequence does not satisfy institutional risk governance requirements. Pre-execution validation means the breach does not settle. That is the governance standard applied to every other delegated capital management arrangement in regulated finance.
A compliance log for mandate validation purposes needs to record every transaction proposed, the specific mandate parameters checked at the time of each proposal, the outcome of each check, every transaction blocked and the specific mandate limit that triggered the block, and every approved transaction. The log must be timestamped, sequential, and exportable in a format that an external auditor can verify independently of the institution or the infrastructure provider. The test is not whether the institution can see its positions. The test is whether it can demonstrate, to an external party, that every past execution decision was within mandate parameters at the time it was made.
Mandate validation only functions as an independent governance mechanism if the party running the validation has no allocation discretion and no protocol referral incentive. If the curator and the infrastructure provider running the validation checks are the same entity, the validation is not independent. The curator would be checking its own decisions against the mandate, with no independent party accountable for the outcome of those checks. Contractual role separation between the curator, the vault operator, and the mandate validation infrastructure is what makes the governance mechanism credible. Legal needs those boundaries to map the arrangement onto existing liability frameworks.
The institutions that have cleared internal approval for DeFi vault deployments, including Société Générale through SG FORGE and Bitwise, have done so by developing or identifying governance infrastructure that addresses these three requirements directly. In each case, the deployment required building or finding a framework that answered the pre-execution control, audit trail, and role separation questions. The existence of those deployments does not indicate that standard vault products satisfy institutional requirements. It indicates that the institutions that moved found infrastructure that does.
Get Advise
P2P.org builds the protection layer that sits between regulated institutions and DeFi execution environments, independently of the curators who manage allocation strategies. If you are evaluating the infrastructure requirements for a DeFi allocation program, talk to our team.
Disclaimer
This article is provided for informational purposes only and does not constitute legal, regulatory, compliance, or investment advice. Regulatory obligations may vary depending on jurisdiction and specific business activities. Readers should consult their own legal and compliance advisors regarding applicable requirements.
<hr><p><strong>SERIES: Institutional Lens</strong></p><p>The Institutional Lens series unpacks the protocol mechanics, infrastructure decisions, and governance considerations that matter most for institutional participants in proof-of-stake networks. Each article is written for professionals operating at the intersection of traditional finance and blockchain infrastructure.</p><p><strong>Previously in the series:</strong> <a href="https://p2p.org/economy/why-institutional-capital-needs-a-protection-layer-in-proof-of-stake-networks/">Why Institutional Capital Needs a Protection Layer in Proof-of-Stake Networks</a></p><h2 id="introduction">Introduction</h2><p>Q1 2026 was not a normal quarter for institutional crypto investment. Three events arrived in sequence that, taken together, represent the most significant structural shift in how large capital holders engage with proof-of-stake networks since Ethereum's transition to proof-of-stake in 2022.</p><p>On February 24, the Ethereum Foundation announced it had begun staking 70,000 ETH from its treasury, completing the process by early April. On March 12, BlackRock launched ETHB, its first staking-integrated ETF, with $107 million in assets and 80% of its ETH already staked on day one. On March 17, the SEC and CFTC jointly confirmed that protocol staking across all four operational models is not a securities transaction, removing the primary regulatory barrier that had kept many institutional compliance teams on the sidelines.</p><p>These were not isolated events. They were the visible surface of a capital flow trend that had been building across the quarter, and they point to where validator demand is heading in the periods ahead. This article maps the Q1 data, identifies the flows that matter most for proof-of-stake infrastructure, and draws out the implications for institutions evaluating or expanding their staking programs.</p><h2 id="learnings-for-busy-readers">Learnings for Busy Readers</h2><p><strong>What this article covers:</strong></p><ul><li>The three structural Q1 events that changed institutional crypto investment dynamics</li><li>Ethereum and Solana capital flow data from Q1 2026</li><li>How the SEC and CFTC March 17 ruling reshaped institutional staking access</li><li>What these flows mean specifically for validator demand</li><li>What institutions should be tracking as Q2 develops</li></ul><p><strong>The core argument:</strong> Q1 2026 confirmed that institutional crypto investment has moved from exploratory to structural in proof-of-stake networks. The capital flows are real, the regulatory barriers are lower than ever, and the infrastructure demand they create is compounding. Validator selection and staking program design are no longer optional decisions for institutions with digital asset exposure.</p><figure class="kg-card kg-image-card kg-card-hascaption"><img src="https://p2p.org/economy/content/images/2026/04/-q1-2026-institutional-capital-flows-validator-demand-timeline.jpg" class="kg-image" alt="A horizontal timeline diagram showing three Q1 2026 institutional crypto investment events: the Ethereum Foundation staking 70,000 ETH on February 24, BlackRock launching ETHB with $107 million on March 12, and the SEC and CFTC joint commodity ruling on March 17, with validator demand implications for each event." loading="lazy" width="2000" height="1304" srcset="https://p2p.org/economy/content/images/size/w600/2026/04/-q1-2026-institutional-capital-flows-validator-demand-timeline.jpg 600w, https://p2p.org/economy/content/images/size/w1000/2026/04/-q1-2026-institutional-capital-flows-validator-demand-timeline.jpg 1000w, https://p2p.org/economy/content/images/size/w1600/2026/04/-q1-2026-institutional-capital-flows-validator-demand-timeline.jpg 1600w, https://p2p.org/economy/content/images/2026/04/-q1-2026-institutional-capital-flows-validator-demand-timeline.jpg 2240w" sizes="(min-width: 720px) 720px"><figcaption><i><em class="italic" style="white-space: pre-wrap;">Three structural events in Q1 2026 reshaped institutional capital flows toward proof-of-stake networks and created compounding demand for validators across Ethereum and Solana.</em></i></figcaption></figure><h2 id="the-three-events-that-defined-q1">The Three Events That Defined Q1</h2><h3 id="the-ethereum-foundation-treasury-pivot">The Ethereum Foundation Treasury Pivot</h3><p>On February 24, 2026, the Ethereum Foundation announced it had begun staking 70,000 ETH from its treasury to fund protocol research, ecosystem development, and community grants. The Foundation completed the process on April 3, staking a final batch of approximately $93 million in ETH and reaching a total staked position of roughly $143 million (Source: <a href="https://www.coindesk.com/markets/2026/04/03/ethereum-foundation-stakes-another-usd93-million-ether-reaching-its-70-000-eth-target?ref=p2p.org">CoinDesk</a>).</p><p>The significance of this event extends well beyond the ETH amount. The Ethereum Foundation had historically funded operations by selling ETH, a practice that generated consistent community criticism and periodic price pressure. The staking approach replaces selling with earning, generating an estimated $3.9 million to $5.4 million annually at current institutional staking rates, funding protocol research, ecosystem grants, and operations without requiring periodic ETH sales (Source: <a href="https://www.coindesk.com/markets/2026/04/03/ethereum-foundation-stakes-another-usd93-million-ether-reaching-its-70-000-eth-target?ref=p2p.org">CoinDesk</a>).</p><p>The staking infrastructure itself is notable for institutional readers. The Foundation used Dirk and Vouch, open-source distributed validator tools originally developed by Attestant and now maintained by Bitwise Onchain Solutions, prioritising client diversity and distributed validator operations. This reflects a non-custodial, multi-jurisdiction signing architecture that reduces single points of failure, a design principle directly relevant to any institutional staking program (Source: <a href="https://www.coindesk.com/business/2026/02/24/putting-the-treasury-to-work-the-ethereum-foundation-just-staked-70-000-eth-to-fund-its-future?ref=p2p.org">CoinDesk</a>).</p><p>For corporate treasury teams and nonprofit organisations holding digital assets, the Ethereum Foundation's move serves as a reference implementation: non-custodial, transparent, using distributed validator tooling, and directing rewards back to operational funding.</p><h3 id="blackrock-ethb-staking-inside-a-regulated-product">BlackRock ETHB: Staking Inside a Regulated Product</h3><p>On March 12, BlackRock launched the iShares Staked Ethereum Trust ETF (ETHB) on Nasdaq, the firm's first crypto fund to incorporate staking and the first yield-generating crypto ETF from the world's largest asset manager. ETHB debuted with $107 million in seed assets and approximately 80% of its ETH already staked on-chain on day one (Source: <a href="https://www.coindesk.com/markets/2026/03/12/blackrock-debuts-staked-ether-etf-as-demand-grows-for-yield-in-crypto-funds?ref=p2p.org">CoinDesk</a>).</p><p>Under normal market conditions, ETHB stakes between 70% and 95% of its ETH holdings through institutional validators. Investors receive approximately 82% of gross staking rewards, distributed monthly, with BlackRock and its service providers retaining 18% as a staking fee. The fund charges a 0.25% sponsor fee, discounted to 0.12% for the first year on the first $2.5 billion in assets (Source: <a href="https://www.blackrock.com/us/individual/products/348532/ishares-staked-ethereum-trust-etf?ref=p2p.org">BlackRock</a>).</p><p>ETHB is structurally significant for validator demand in a specific way. Every dollar flowing into ETHB creates a corresponding demand for institutional-grade, non-custodial validator operations. The validator infrastructure layer is no longer a back-end service. It is embedded in a regulated, publicly traded product managed by the world's largest asset manager. As ETF inflows compound, so does the demand for the validator infrastructure that secures those positions (Source: <a href="https://www.fintechweekly.com/news/blackrock-ibit-bitcoin-etf-inflows-ethb-staked-ethereum-nasdaq-march-2026?ref=p2p.org">FinTech Weekly</a>).</p><h3 id="the-march-17-sec-and-cftc-joint-interpretation">The March 17 SEC and CFTC Joint Interpretation</h3><p>The regulatory clearing event of Q1 arrived on March 17, when the SEC and CFTC jointly confirmed that protocol staking across solo, self-custodial, custodial, and liquid staking models does not constitute a securities transaction. The ruling explicitly confirmed that staking rewards do not create a securities-type relationship, applying to all proof-of-stake assets in the named 16 and validating existing staking products, including ETFs and exchange-based products. The commodity classification means compliance departments no longer have grounds to restrict exposure based on securities risk (Source: <a href="https://phemex.com/blogs/sec-ruling-crypto-etfs-staking?ref=p2p.org">Phemex</a>).</p><p>For institutional staking programs, this ruling is the most consequential regulatory event since Ethereum's Merge. It does not just clarify existing products. It removes the legal basis for the compliance restrictions that had prevented many institutions from building multi-chain staking programs across assets like SOL, ADA, and DOT. The addressable market for institutional staking infrastructure expanded materially on March 17.</p><h2 id="ethereum-the-capital-flow-picture">Ethereum: The Capital Flow Picture</h2><p>The Ethereum staking ecosystem entered Q1 2026 with significant momentum and closed the quarter with institutional participation at record levels.</p><p>Ethereum's staking ratio reached a record 31.1% of total supply in March 2026, with institutional staking demand rising as BlackRock's staked Ethereum trust reached approximately $254 million in AUM in its first week. Base ETH staking rewards generally range from 3% to 4% annually, while restaking incentives can temporarily lift combined yields above 8% to 15% (Source: <a href="https://coinlaw.io/cryptocurrency-staking-statistics/?ref=p2p.org">CoinLaw</a>).</p><p>Understanding the Ethereum reward structure is important for institutions setting performance expectations. Ethereum staking rewards come from two distinct sources: consensus layer rewards, which are protocol-issued and relatively predictable, accruing each epoch for attestations, block proposals, and sync committee participation; and execution layer rewards, which come from user priority fees and MEV and are inherently variable depending on on-chain activity levels. Consensus layer rewards currently represent the large majority of total validator rewards, with execution layer rewards being the smaller but more variable component. The ETH.STORE benchmark, published daily by <a href="https://beaconcha.in/ethstore?ref=p2p.org">beaconcha.in</a>, is the institutional reference rate for Ethereum staking yield comparison across providers (Source: <a href="https://beaconcha.in/ethstore?ref=p2p.org">beaconcha.in</a>).</p><p>The restaking ecosystem also continued its expansion in Q1. The Ethereum restaking ecosystem reached a total value locked of $16.257 billion as of early 2026, with 4,650,055 ETH utilised within restaking frameworks providing cryptoeconomic security for Actively Validated Services. EigenLayer dominates the sector with $15.258 billion in TVL and 4,364,467 ETH, commanding a 93.9% market share (Source: <a href="https://www.datawallet.com/crypto/ethereum-staking-statistics-and-trends?ref=p2p.org">Datawallet</a>).</p><p>Restaking represents an additional layer of validator demand that compounds on top of base staking flows. As institutions deploy into restaking, the infrastructure requirements extend beyond standard validator operations to include actively validated service participation, slashing risk management across multiple protocols, and more complex reporting requirements.</p><h2 id="solana-etf-flows-and-institutional-staking-surge">Solana: ETF Flows and Institutional Staking Surge</h2><p>Solana's Q1 capital flow story is distinct from Ethereum's and in some ways, more striking, given that Solana ETFs only launched in October 2025.</p><p>Cumulative inflows into U.S. Solana ETFs passed $900 million by early March 2026, with Goldman Sachs disclosing $108 million in SOL ETF holdings as of April 2026. Solana ETFs launched with staking built in from day one, something Bitcoin and Ethereum ETFs did not offer at launch (Source: <a href="https://usethebitcoin.com/guides/solana-etf-approval/?ref=p2p.org">UseTheBitcoin</a>).</p><p>The staking-integrated structure of Solana ETFs creates an immediate and direct validator demand signal. Bitwise's BSOL stakes 100% of its SOL holdings, targeting average annual staking rewards above 7%. Solana staking rewards historically range between 5% and 7% per annum, paid once per epoch lasting around two days. The yield is variable because the calculation depends on Solana's inflation rate and the total active staked SOL, both of which change continually (Source: <a href="https://coinshares.com/insights/knowledge/solana-staking-explained/?ref=p2p.org">CoinShares</a>). Solana's inflation follows a disinflationary schedule, starting at 8% annually and decreasing by 15% per year until reaching a long-term fixed inflation rate of 1.5% (Source: <a href="https://solana.com/staking?ref=p2p.org">Solana.com</a>).</p><p>The institutional staking surge on Solana extended beyond ETF products. Institutional capital is increasingly viewing Solana as a high-speed execution layer for internet capital markets, with over $1 billion in ETF inflows recorded by early 2026. This shift is underpinned by a TVL exceeding $11 billion and the deployment of enterprise tools for tokenising real-world assets (Source: <a href="https://www.ainvest.com/news/solana-network-stabilizes-institutional-staking-surge-price-correction-2604/?ref=p2p.org">AInvest</a>).</p><p>The Solana capital flow picture also carried a structural warning. The validator count on Solana dropped from approximately 2,500 to under 800 in 2026, raising concerns about centralisation and the long-term health of the network's consensus mechanism (Source: <a href="https://www.ainvest.com/news/solana-network-stabilizes-institutional-staking-surge-price-correction-2604/?ref=p2p.org">AInvest</a>). For institutions selecting Solana validator infrastructure, this concentration trend is a material due diligence consideration. Geographic and operator diversity in delegation decisions is not just an ideological position on decentralisation. It is a risk management requirement that directly affects the resilience of the assets being staked.</p><h2 id="what-these-flows-mean-for-validator-demand">What These Flows Mean for Validator Demand</h2><p>The Q1 data points to three structural implications for validator demand that institutional teams should factor into their staking program design.</p><p><strong>Implication 1: ETF inflows create compounding validator demand</strong></p><p>Every staking-integrated ETF product creates a direct and persistent demand for validator infrastructure. As ETHB, BSOL, VSOL, and future products attract inflows, the validator operations supporting those products must scale with them. Staking-integrated ETFs now account for more than 40% of all institutional Ethereum investments in early 2026, up from nearly zero just 18 months prior (Source: <a href="https://blockeden.xyz/blog/2026/03/12/blackrock-ethb-staked-ethereum-etf-defi-yield/?ref=p2p.org">BlockEden</a>). The institutions best positioned to serve this demand are those with the operational track record, geographic distribution, and reporting capabilities that regulated ETF products require.</p><p><strong>Implication 2: Corporate treasury staking is becoming a standard practice</strong></p><p>An Intertrust survey of 100 global hedge fund CFOs found a target digital asset allocation of 7.2% by 2026, representing approximately $312 billion across the sector, with North American funds projecting 10.6% exposure and UK and European funds projecting 6.8% (Source: <a href="https://www.coindesk.com/markets/2021/06/15/hedge-funds-see-72-of-assets-in-crypto-by-2026-report?ref=p2p.org">CoinDesk</a>). The Ethereum Foundation's treasury staking initiative and BlackRock's ETHB launch signal that converting dormant treasury holdings into productive staked positions is becoming a standard treasury management function, not an experimental one.</p><p>For institutions currently holding unstaked digital assets, the Q1 signals point to an accelerating competitive disadvantage. Staking transforms passive balance sheet exposure into protocol-native reward participation. Every quarter of unstaked holdings on a proof-of-stake network is a quarter of protocol reward dilution.</p><p><strong>Implication 3: The March 17 ruling expands the multi-chain staking mandate</strong></p><p>Before March 17, many institutional mandates restricted staking activity to Ethereum because it was the only proof-of-stake asset with an unambiguous legal status in the United States. The SEC and CFTC commodity classification of 16 additional assets, including SOL, ADA, DOT, and XRP, removes that restriction. Institutions that had built Ethereum-only staking programs now have the legal basis to evaluate multi-chain staking programs.</p><p>Multi-chain staking programs require infrastructure providers with consistent operational standards across networks, not just depth on a single chain. This is one of the most direct implications of Q1's regulatory development for validator selection criteria.</p><p><a href="http://p2p.org/?ref=p2p.org">P2P.org</a> operates non-custodial validator infrastructure across more than 40 proof-of-stake networks, including <a href="https://p2p.org/networks/ethereum?ref=p2p.org">Ethereum</a> and <a href="https://p2p.org/networks/solana?ref=p2p.org">Solana</a>, with consistent operational architecture and institutional-grade reporting across each. For teams evaluating multi-chain staking programs, our <a href="https://docs.p2p.org/?ref=p2p.org">technical documentation</a> provides integration and reporting details for each supported network.</p><hr><blockquote><strong>Evaluating your institutional staking program for Q2 and beyond?</strong> <a href="http://p2p.org/?ref=p2p.org">P2P.org</a> provides non-custodial, validator-level staking across 40+ proof-of-stake networks with SOC 2 Type II certified operational controls and full reward attribution reporting. <a href="https://p2p.org/networks/ethereum?ref=p2p.org">Explore P2P.org Staking Infrastructure</a> or <a href="https://www.p2p.org/?ref=p2p.org#form">Request a Meeting</a></blockquote><hr><h2 id="what-to-watch-in-q2">What to Watch in Q2</h2><p>Q1 established the structural conditions. Q2 will test whether they compound or stabilise. The following signals are the most relevant for institutional staking programs.</p><p><strong>CLARITY Act Senate markup.</strong> Targeted for late April, the Senate Banking Committee markup is the next legislative step for the bill that would codify the March 17 SEC and CFTC interpretation into statute. The passage would convert persuasive regulatory guidance into binding law, permanently settling the legal classification of staking as a non-securities activity. The window is narrow: if the bill does not reach the Senate floor before May, it may not advance before midterm election pressures close the legislative calendar.</p><p><strong>Solana ETF staking inflow trajectory.</strong> Solana ETFs surpassed $1 billion in cumulative inflows faster than most analysts projected. Q2 will show whether that pace is sustained and whether additional staking-enabled products launch for other newly classified commodities, including ADA and DOT. Each new staking ETF product creates additional validator infrastructure demand.</p><p><strong>Alpenglow deployment on Solana.</strong> The Alpenglow upgrade, which eliminates validator voting fees and reduces transaction finality from approximately 12.8 seconds to 100 to 150 milliseconds, is scheduled for deployment in 2026. Its activation will directly affect Solana validator economics, improving net reward rates for delegators without changing the risk posture of native staking programs.</p><p><strong>ETH staking ETF product expansion.</strong> With ETHB validated and the commodity ruling in place, additional staking-integrated ETH products are likely to follow from other issuers. Each new product adds to the base of ETF-linked validator demand on Ethereum.</p><h2 id="due-diligence-checklist-evaluating-your-staking-program-in-light-of-q1">Due Diligence Checklist: Evaluating Your Staking Program in Light of Q1</h2><p>For institutions reviewing or expanding staking programs following Q1's developments:</p><ul><li>[ ] Has your mandate been updated to reflect the March 17 SEC and CFTC commodity classification for multi-chain staking?</li><li>[ ] Have you evaluated staking opportunities across the 16 newly classified digital commodities, not only Ethereum?</li><li>[ ] Is your validator infrastructure provider operating consistently across the chains relevant to your portfolio?</li><li>[ ] Are you capturing validator-level reward attribution data compatible with your accounting and audit requirements?</li><li>[ ] Have you assessed the validator concentration risk on Solana and its implications for your delegation strategy?</li><li>[ ] Is your liquidity management framework updated for the unbonding timelines of any new networks added to your program?</li><li>[ ] Does your staking program have a governance participation policy for protocol upgrade events, including Alpenglow?</li></ul><h2 id="key-takeaway">Key Takeaway</h2><p>Q1 2026 produced three structural events for institutional crypto investment in proof-of-stake networks: the Ethereum Foundation's treasury staking pivot, completing at $143 million; BlackRock's ETHB launch, embedding validator demand inside a regulated ETF product; and the SEC and CFTC's joint commodity classification of 16 digital assets, including SOL. Together, they establish that institutional staking has crossed from exploratory to structural, that the regulatory barriers to multi-chain staking programs are substantially lower than they were three months ago, and that the validator infrastructure demand created by ETF flows is compounding with each new product launch.</p><p>For institutions currently holding unstaked digital assets on proof-of-stake networks, Q1's signals point in one direction. The program design decisions made now will define the institution's position in the institutional staking landscape for the periods ahead.</p><h2 id="frequently-asked-questions-faqs">Frequently Asked Questions (FAQs)</h2><h3 id="what-were-the-most-significant-institutional-crypto-investment-events-of-q1-2026"><strong>What were the most significant institutional crypto investment events of Q1 2026?</strong></h3><p>Three events stand out. The Ethereum Foundation completed the staking of 70,000 ETH from its treasury, worth approximately $143 million, replacing its previous practice of selling ETH to fund operations. BlackRock launched ETHB, its first staking-integrated ETF, with $107 million in assets at launch. The SEC and CFTC jointly confirmed on March 17 that protocol staking across all four operational models is not a securities transaction, removing the primary legal barrier to institutional multi-chain staking programs.</p><h3 id="how-does-the-sec-and-cftc-march-17-ruling-affect-institutional-staking-programs"><strong>How does the SEC and CFTC March 17 ruling affect institutional staking programs?</strong></h3><p>The ruling explicitly confirmed that protocol staking does not constitute a securities transaction for any of the 16 named digital commodities, including SOL, ADA, DOT, XRP, and ETH. For institutions that had restricted staking activity to Ethereum because of its clearer legal status, the ruling provides the legal basis to build multi-chain staking programs. Compliance departments previously blocking exposure to altcoin staking on securities grounds now need to update their internal guidance.</p><h3 id="what-do-solana-etf-inflows-signal-for-validator-demand"><strong>What do Solana ETF inflows signal for validator demand?</strong></h3><p>Solana ETFs surpassed $1 billion in cumulative inflows by early March 2026, significantly faster than projections. Because most Solana ETF products stake 100% of their holdings, every dollar of ETF inflow creates direct demand for validator infrastructure. Goldman Sachs disclosed $108 million in SOL ETF holdings as of April 2026, signalling that major institutional allocators have taken visible positions (Source: <a href="https://usethebitcoin.com/guides/solana-etf-approval/?ref=p2p.org">UseTheBitcoin</a>).</p><h3 id="what-is-the-ethereum-foundation-staking-initiative-and-why-does-it-matter-for-institutions"><strong>What is the Ethereum Foundation staking initiative, and why does it matter for institutions?</strong></h3><p>The Ethereum Foundation staked approximately 70,000 ETH between February and April 2026, converting a portion of its treasury from a passive holding into a yield-generating staked position. The initiative generates an estimated $3.9 million to $5.4 million annually in protocol-generated rewards, reducing the Foundation's need to sell ETH to fund operations. For corporate treasury teams, it serves as a reference implementation for non-custodial treasury staking at scale using distributed validator infrastructure (Source: <a href="https://www.coindesk.com/markets/2026/04/03/ethereum-foundation-stakes-another-usd93-million-ether-reaching-its-70-000-eth-target?ref=p2p.org">CoinDesk</a>).</p><h3 id="what-is-the-validator-concentration-risk-on-solana-and-why-does-it-matter"><strong>What is the validator concentration risk on Solana, and why does it matter?</strong></h3><p>The Solana validator count dropped from approximately 2,500 to under 800 in 2026, raising centralisation concerns. For institutions delegating to Solana validators, this concentration trend means that validator selection and geographic distribution in delegation decisions carry more risk management significance than they did previously. Diversifying delegation across independent operators in different geographic regions reduces exposure to correlated failure and network centralisation risk (Source: <a href="https://www.ainvest.com/news/solana-network-stabilizes-institutional-staking-surge-price-correction-2604/?ref=p2p.org">AInvest</a>).</p><h3 id="what-should-institutions-monitor-in-q2-2026-for-staking-program-decisions"><strong>What should institutions monitor in Q2 2026 for staking program decisions?</strong></h3><p>The most important signals are the CLARITY Act Senate markup targeted for late April, Solana ETF inflow trajectory and potential new staking-enabled product launches for other newly classified commodities, Alpenglow deployment on Solana and its impact on validator economics, and ETH staking ETF product expansion from additional issuers following the ETHB precedent.</p><hr><p><em>[Protocol-generated rewards are determined by network conditions and are variable. </em><a href="http://p2p.org/?ref=p2p.org"><em>P2P.org</em></a><em> does not control or set reward rates. Slashing risks are protocol-defined and client-borne. Operational safeguards are implemented to reduce slashing exposure but do not eliminate protocol-level risk.]</em></p>
from p2p validator
<p>on-chain<strong>Series: DeFi Dispatch</strong></p><p>DeFi Dispatch is P2P.org's twice-monthly roundup of DeFi developments for institutional participants. Each edition covers the signals that matter for asset managers, custodians, hedge funds, ETF issuers, exchanges, and staking teams operating at the intersection of traditional and on-chain finance.</p><p>Legal Layer, April 2026. This month's top regulatory developments for institutional participants in the digital asset ecosystem:</p><p>👉 <strong>Subscribe to our newsletter </strong>at the bottom of this page to receive a monthly summary of the latest DeFi and staking developments, curated for institutional participants.</p><p><em>Missed the previous edition? Catch up here: </em><a href="https://p2p.org/economy/defi-dispatch-defi-news-april-2026-issue-1/"><em>DeFi Dispatch: DeFi News and Signals April 2026 (Issue 1)</em></a></p><h2 id="quick-learnings-for-busy-readers">Quick Learnings for Busy Readers</h2><p>Short on time? Here are the key takeaways. For the full analysis, continue reading below.</p><p>The mid-April period brought five developments that institutional participants in DeFi and staking infrastructure should track closely.</p><ol><li>A $292 million exploit of KelpDAO's rsETH token cascaded across DeFi lending markets, driving a $14 billion TVL decline and exposing how cross-chain collateral concentration creates systemic contagion pathways that move faster than any monitoring system can catch.</li><li>Charles Schwab launched direct spot Bitcoin and Ethereum trading for retail and advisory clients, a structurally significant moment that embeds digital asset access into the mainstream brokerage infrastructure that institutional allocators already use.</li><li>Nomura's 2026 Digital Assets Institutional Investor Survey found that nearly 80% of institutions plan to allocate 2% to 5% of AUM to digital assets, with over two-thirds specifically targeting DeFi mechanisms, including staking, lending, and tokenized assets.</li><li>Circle launched CPN Managed Payments, a full-stack stablecoin settlement platform for institutions, accelerating the infrastructure layer that connects regulated payment rails to on-chain capital markets.</li><li>Research from FinTech Weekly highlighted that 83% to 95% of deposited DeFi liquidity sits idle at any given moment, signalling a structural shift toward capital efficiency metrics over raw TVL as the primary measure of protocol health.</li></ol><h2 id="story-1-kelpdao-exploit-triggers-14-billion-defi-contagion">Story 1: KelpDAO Exploit Triggers $14 Billion DeFi Contagion</h2><p>On April 19, a $292 million exploit of KelpDAO's rsETH token cascaded through DeFi lending markets, driving total value locked across DeFi protocols from approximately $99 billion to $85 billion over 48 hours, the lowest level in a year and roughly 50% below the October 2025 peaks. Aave alone saw approximately $10 billion in deposits exit over the same period.</p><p>The attack exploited a misconfigured cross-chain verification setup in LayerZero-based bridge infrastructure. Because rsETH was widely used as collateral across multiple lending protocols, including Aave, Euler, and Sentora, the depegging of the stolen tokens created bad debt positions across the ecosystem simultaneously. Users rushed to withdraw funds across platforms with no direct exposure to the exploit, amplifying the contagion.</p><p>The failure mode is architecturally instructive. The rsETH token's integration across multiple protocols meant that a single verification gap in one piece of bridge infrastructure created simultaneous exposure across the lending ecosystem. No individual protocol's risk parameters could contain a shock that originated in the collateral layer shared across all of them.</p><p>For institutional allocators evaluating DeFi vault exposure, the KelpDAO episode illustrates a category of risk that due diligence on individual protocols does not capture: systemic collateral concentration risk, where a widely integrated token becomes a single point of failure for the infrastructure that depends on it. The absence of an independent pre-execution validation layer means institutions discover this exposure only after it has already settled on-chain.</p><p><em>Source: CoinDesk, TheStreet Crypto, April 2026.</em></p><h2 id="story-2-charles-schwab-launches-spot-bitcoin-and-ethereum-trading">Story 2: Charles Schwab Launches Spot Bitcoin and Ethereum Trading</h2><p>Charles Schwab launched direct spot trading for Bitcoin and Ethereum across its retail brokerage platform in April 2026, enabling clients to buy and sell the two largest digital assets alongside equities, fixed income, and other asset classes within a single portfolio framework.</p><p>The significance for institutional participants is structural rather than product-level. Schwab manages one of the largest advisor-distributed asset pools in the United States. Its entry into direct spot crypto trading means that registered investment advisors using the Schwab platform can now include digital assets in client portfolios using the same custody, reporting, and compliance infrastructure they apply to every other asset class. This is a distribution event, not just a product launch.</p><p>The move accelerates a dynamic that has been building since the Bitcoin ETF approvals in early 2024: digital assets are being embedded into the infrastructure that institutional capital already uses, rather than requiring institutions to build parallel infrastructure to access them. Each major brokerage entry narrows the gap between where institutional allocators operate and where digital asset exposure lives.</p><p>For staking and DeFi infrastructure providers, the expansion of institutional digital asset access through mainstream brokerage channels increases the pool of capital that may eventually seek on-chain yield strategies, as familiarity with Bitcoin and Ethereum exposure is typically a precondition for engagement with more complex on-chain strategies.</p><p><em>Source: HedgeCo Insights, April 2026.</em></p><h2 id="story-3-nomura-survey-finds-80-of-institutions-plan-digital-asset-allocations">Story 3: Nomura Survey Finds 80% of Institutions Plan Digital Asset Allocations</h2><p>Nomura Securities released its 2026 Digital Assets Institutional Investor Survey in mid-April, covering institutional investors and family offices with aggregate assets under management exceeding $600 billion. The findings represent the clearest institutional intent signal of the year to date.</p><p>Nearly 80% of respondents plan to allocate 2% to 5% of total AUM to digital assets. 65% view digital assets as a diversification tool comparable to equities, fixed income, and commodities. Over two-thirds of respondents plan to pursue returns through DeFi mechanisms specifically, including staking, lending, and tokenized assets. 65% expressed interest in lending and tokenized asset strategies. 63% are evaluating derivatives and stablecoins.</p><p>The DeFi-specific intent figure is the most significant data point for infrastructure providers. Intent to allocate through DeFi mechanisms is materially higher than current engagement levels, which the EY-Parthenon and Coinbase survey earlier this year placed at 24%. The gap between intent and deployment remains large, and the infrastructure gap, the absence of pre-execution controls, exportable compliance logs, and defined role separation, is a primary reason for it.</p><p>The Nomura survey also found that 63% of respondents view stablecoins as having practical use cases for cash management, cross-border payments, and tokenized asset investment, with institutional-issued stablecoins being the most trusted category.</p><p><em>Source: Nomura Securities 2026 Digital Assets Institutional Investor Survey, via Bitget News, April 2026.</em></p><h2 id="story-4-circle-launches-cpn-managed-payments-for-institutional-stablecoin-settlement">Story 4: Circle Launches CPN Managed Payments for Institutional Stablecoin Settlement</h2><p>Circle launched CPN Managed Payments in April 2026, a full-stack platform designed to help financial institutions adopt and scale stablecoin-based settlement infrastructure. The platform covers the full institutional payment lifecycle from wallet infrastructure through merchant acceptance and cross-border settlement.</p><p>The launch reflects the maturing architecture of the stablecoin settlement layer. Following the passage of the GENIUS Act in July 2025 and the subsequent rollout of implementation rules by Treasury, FinCEN, OFAC, FDIC, and OCC, the regulatory framework for institutional stablecoin use is now defined enough for infrastructure providers to build production-grade solutions against it. CPN Managed Payments is the first major full-stack institutional offering to follow that framework rollout directly.</p><p>For institutions building on-chain capital programs, stablecoin settlement infrastructure is the connective tissue between regulated payment rails and on-chain allocation strategies. An institution that can settle in USDC through a compliant, auditable infrastructure layer has the foundational plumbing that makes interaction with DeFi lending protocols operationally viable. The Circle launch accelerates that infrastructure layer.</p><p>The development also connects directly to the Nomura survey finding that 63% of institutional respondents see stablecoins as practical tools for cash management and tokenized asset investment. The intent is to meet the infrastructure timeline on a compressed schedule.</p><p><em>Source: Zeeve Institutional Tokenization Report, April 2026.</em></p><h2 id="story-5-capital-efficiency-emerges-as-the-new-defi-benchmark">Story 5: Capital Efficiency Emerges as the New DeFi Benchmark</h2><p>Research published by FinTech Weekly in mid-April highlighted a structural problem in DeFi that institutional capital is beginning to price: between 83% and 95% of deposited liquidity across major DeFi protocols sits idle at any given moment, generating no fees and producing no meaningful protocol revenue relative to assets deployed.</p><p>The piece introduced revenue density as the metric institutional allocators are beginning to apply: the ratio of genuine protocol revenue to the capital required to generate it. A protocol generating $10 million in annual fees from $200 million in active liquidity is doing something fundamentally different from one generating $3 million from $2 billion in deposits. The first is a functioning market. The second, to use the article's framing, is a parking lot.</p><p>This shift in the evaluation framework matters for institutional DeFi infrastructure for two reasons. First, it signals that the TVL-maximisation incentives that have defined curator behaviour in DeFi vaults are coming under pressure from allocators who apply capital efficiency metrics rather than headline TVL as their primary evaluation criteria. Second, it suggests that the protocols and infrastructure providers that demonstrate real yield from real usage will be better positioned to attract institutional capital as it moves from intent to deployment.</p><p>The capital efficiency signal also reinforces the case for pre-execution mandate validation in vault infrastructure. Institutions that cannot verify where their capital is deployed at any given moment cannot calculate revenue density. Governance architecture and performance measurement are the same problem viewed from different angles.</p><p><em>Source: FinTech Weekly, April 2026.</em></p><h2 id="key-takeaways-for-asset-managers-custodians-hedge-funds-etf-issuers-exchanges-and-staking-teams">Key Takeaways for Asset Managers, Custodians, Hedge Funds, ETF Issuers, Exchanges, and Staking Teams</h2><p>The mid-April period surfaces five converging signals for institutional participants in onchain infrastructure:</p><ol><li>Systemic collateral concentration risk is now a documented and live concern, not a theoretical one. The KelpDAO episode showed that cross-chain collateral integration creates contagion pathways that move faster than protocol-level monitoring can catch.</li><li>Mainstream brokerage infrastructure is embedding digital asset access, expanding the institutional capital base that may eventually seek on-chain yield strategies as familiarity with Bitcoin and Ethereum exposure develops.</li><li>Institutional intent to allocate through DeFi mechanisms, including staking and lending is materially higher than current deployment levels, with the infrastructure gap remaining the primary explanation for the difference.</li><li>Stablecoin settlement infrastructure is reaching institutional production readiness following regulatory framework clarity, accelerating the connective tissue between regulated payment rails and on-chain capital markets.</li><li>Capital efficiency is replacing TVL as the primary institutional performance benchmark for DeFi protocols, with implications for how curator incentives and vault governance will be evaluated by allocators applying traditional asset management frameworks.</li></ol><hr><p>👉 <strong>Subscribe to our newsletter</strong> at the bottom of this page to receive a monthly summary of the latest DeFi and staking developments, curated for institutional participants. Or follow us on <a href="https://linkedin.com/company/p2p-org?ref=p2p.org">LinkedIn</a> and <a href="https://twitter.com/p2pvalidator?ref=p2p.org">X</a> to stay updated when new DeFi Dispatch editions are published.</p>
from p2p validator