Subscribe to P2P-economy
Stay up to date! Get all the latest & greatest posts delivered straight to your inbox
SubscribeSeries: DeFi Infrastructure for Institutions
P2P.org's content series for regulated institutions evaluating on-chain capital allocation. Each article addresses a specific infrastructure, governance, or compliance dimension that determines whether a DeFi allocation can clear institutional approval and operate within mandate.
This article opens a three-part sequence on the structural gap between DeFi vault architecture and institutional requirements. Part one covers why most vaults were not built for institutional risk tolerance. Part two examines the conflict of interest at the heart of vault design. Part three explains what mandate validation at execution actually means for regulated allocators.
Already familiar with the institutional staking landscape? Read our latest Institutional Lens piece: Why Institutional Capital Needs a Protection Layer in Proof-of-Stake Networks
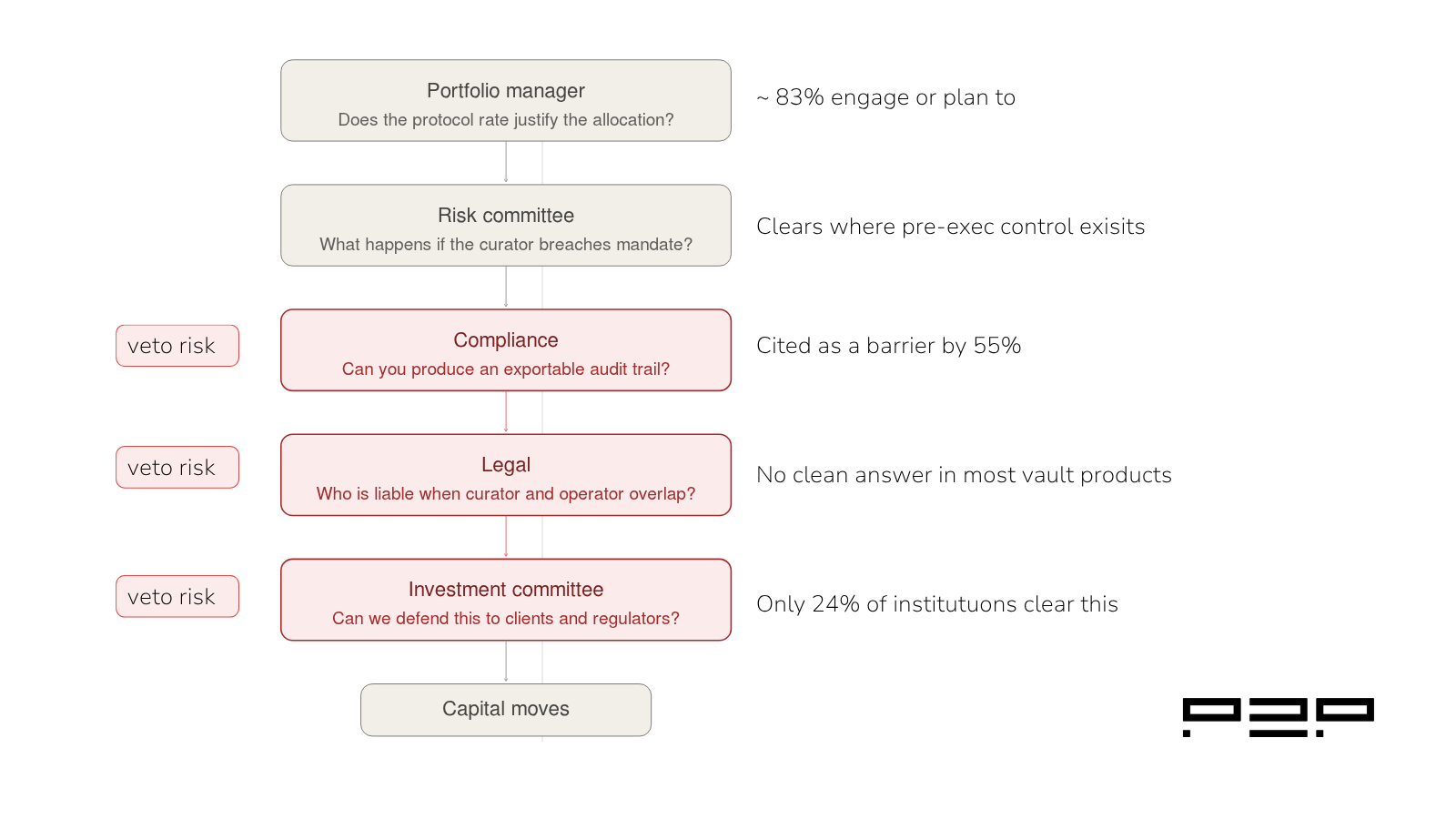
The numbers signal a market that should be moving. A January 2025 survey of 352 institutional investors by EY-Parthenon and Coinbase found that 83% plan to increase crypto allocations, with 59% intending to commit more than 5% of their AUM. Yet only 24% currently engage with DeFi. The gap between intention and deployment is not primarily a protocol problem. The protocols work. DeFi total value locked surpassed $89 billion in 2025. The lending infrastructure is mature, audited, and increasingly well understood.
The gap is architectural. Most DeFi vault products were designed for retail capital, and the governance assumptions built into that design create structural problems that regulated institutions cannot work around. Those problems do not show up in yield figures or protocol audits. They show up the moment a compliance team, a risk committee, or a legal function begins asking the questions they are required to ask before capital moves.
This article explains what those problems are, why they are architectural rather than superficial, and what the institutional requirement actually looks like in practice.
Short on time? Here are the key takeaways. For the full analysis and supporting data, continue reading below.
To understand the gap, it helps to understand what DeFi vaults were originally designed to do.
The vault model emerged as a solution to a genuine problem: retail capital wanted access to DeFi protocol yields without the operational complexity of managing positions manually across multiple protocols. A vault abstracts that complexity. A depositor commits capital, a curator manages the allocation strategy, and the vault smart contract executes the rebalances automatically.
That design is highly effective for its intended use case. Morpho's curated vault system holds roughly $5.8 billion in total value locked. Kamino manages $2.36 billion on Solana. The market has validated the product architecture at scale.
But the risk framework built into that architecture reflects retail assumptions. In a retail context, the depositor evaluates the curator's track record and the protocol's audit history, accepts the smart contract risk, and monitors the position through a dashboard. The governance question is essentially: do I trust this curator? The compliance question does not exist. The audit trail requirement does not exist. The mandate validation requirement does not exist.
Regulated institutions do not operate in that framework. They operate in one where capital allocation decisions are governed by documented mandates, reviewed by multiple internal functions, and subject to post-hoc audit by external parties. The gap between those two frameworks is not a gap in risk tolerance alone. It is a gap in what the infrastructure is required to produce.
In most vault architectures, the curator decides the allocation strategy and the smart contract executes it. There is no independent layer between the curator's decision and on-chain settlement that validates whether the execution is within the client's mandate parameters before it occurs.
For a retail depositor, this is acceptable. The depositor has opted into the curator's strategy and accepts the execution as designed.
For a regulated institution, it is a structural problem. The same EY-Parthenon and Coinbase survey found that compliance risk was cited by 55% of institutional investors as a barrier to DeFi engagement, and lack of internal expertise by 51%. These are not concerns about whether DeFi is legal. They are concerns about whether institutions can operationalize DeFi exposure within their existing risk frameworks. A position that breaches a concentration limit settles on-chain before the risk committee knows it happened. The institution discovers the breach through portfolio monitoring after the fact. That sequence does not clear a risk committee.
Pre-execution mandate validation means every curator transaction is checked against the client's parameters before it settles: concentration limits, protocol allowlists, slippage thresholds, and oracle integrity checks. The breach does not settle. It is blocked. That is a fundamentally different infrastructure function from monitoring, and most vault products do not have it.
A vault dashboard shows current positions, historical performance, and rebalancing history. That is monitoring infrastructure. It is useful for portfolio management. It is not an audit trail.
An audit trail is a sequential log of every execution decision, the parameters checked at the time of each execution, every transaction blocked and the mandate limit that triggered the block, in a format that can be exported and verified independently by an external auditor. The difference matters because auditors and regulators are not checking whether the positions look correct now. They are checking whether the institution can demonstrate that every decision was within mandate parameters at the time it was made.
Most vault products cannot produce that demonstration because the infrastructure to generate it was never built. The design assumption was that on-chain transparency, the ability to verify every transaction on a block explorer, was equivalent to an audit trail. For regulatory purposes, it is not.
Academic analysis of on-chain lending from October 2024 to November 2025 across six major lending systems found that a small set of curators intermediates a disproportionate share of system total value locked, and that the main locus of risk in DeFi lending has migrated from base protocols to the curator layer, where competing vault managers decide which assets and loans are originated. The researchers argue this shift requires a corresponding upgrade in transparency standards(Source: Institutionalizing Risk Curation in Decentralized Credit, arXiv, December 2025.).
In most vault architectures, the curator who designs the strategy and the operator who manages the infrastructure are either the same entity or operate without contractually separated liability boundaries. For retail capital, this simplifies the relationship. There is one counterparty.
For regulated institutions, it creates an unresolvable legal problem. When something goes wrong, who is liable? The curator who made the allocation decision? The operator who managed the smart contract? If those functions are not contractually separated with explicit liability maps, legal cannot answer the question. And legal, not being able to answer the question, means the allocation does not proceed.
The framework that regulated institutions apply to every other delegated capital management arrangement requires defined counterparty roles with non-overlapping responsibilities. A structure where curator and operator are the same entity, or where their liability boundaries are undefined, does not fit that framework.
The common industry response to the institutional adoption gap has been to add permissioned access layers: KYC-gated pools, whitelisted depositor sets, and compliance-oriented interfaces.
The data on this approach is instructive. As Sygnum Bank noted in its institutional DeFi assessment, at least one permissioned lending product built specifically for regulated institutions held a negligible $50,000 in total value locked despite being architecturally designed to meet institutional compliance requirements. KYC-gated vaults and permissioned lending pools more broadly have not attracted meaningful institutional flows. Sygnum, one of the few regulated digital asset banks, concluded that nearly all inflows continue to come from asset managers, hedge funds, or crypto-native firms with higher risk tolerance, not from the major institutional decision-makers the products were designed to serve.
The reason is that permissioned access addresses the wrong problem. The question institutional due diligence asks is not "can we access this protocol compliantly?" It is "can we demonstrate, after the fact, that our capital was managed within mandate parameters at every point, by a counterparty whose liability is contractually defined?" Access controls do not answer that question. Pre-execution validation, audit trail infrastructure, and role separation do.
Even where regulatory conditions are improving, the resolution institutional decision-makers require is not primarily regulatory. It is architectural.
The institutions that have successfully deployed capital into DeFi protocols have done so by identifying infrastructure that addresses each of the three gaps directly.
Société Générale, through its digital assets division SG FORGE, became the first major global bank to deploy capital into permissionless DeFi, using Morpho protocol vaults on Ethereum mainnet following months of due diligence and a purpose-built institutional risk framework. The methodology developed for that deployment required answering the same three governance questions that stop most institutions: pre-execution controls, audit-compatible reporting, and defined role boundaries.
The infrastructure requirement is not a higher version of what retail vaults provide. It is a different category of function entirely: a protection layer that sits between the institution and the execution environment, independent of the curator, validating every transaction before it settles and producing a compliance log that can survive an external audit.
Institutional crypto asset management is projected to grow at a 25.5% compound annual growth rate, reaching $5.53 billion by 2030, with that growth contingent on regulatory clarity and advances in custody standards. The custody and reporting standards that growth depends on are not being built at the protocol layer. They are being built at the protection layer above it.
The institutional DeFi adoption gap is not primarily a yield problem, a regulatory problem, or a protocol maturity problem. It is a governance architecture problem.
DeFi vaults were built for retail capital, and the assumptions built into that architecture do not accommodate the pre-execution controls, audit trail infrastructure, or role separation that regulated institutions require as standard. Permissioned access addresses the access question. It does not address the governance question. And the governance question is the one that determines whether an allocation clears internal approval.
The infrastructure that closes the gap is not an extension of what current vault products provide. It is a new layer entirely.
Next in this series: The Conflict of Interest Problem at the Heart of DeFi Vault Design (soon out).
A DeFi vault allocates capital according to a curator's strategy and executes rebalances automatically through a smart contract. Institutional-grade vault infrastructure adds a protection layer above that execution environment: pre-execution mandate validation that checks every transaction against the client's parameters before settlement, an exportable compliance log that produces an audit-compatible record of every execution decision, and contractually defined role separation between the curator, the operator, and the infrastructure provider. These are not enhancements to the vault product. They are a separate infrastructure function.
Because post-execution monitoring does not satisfy institutional risk governance requirements. If a vault rebalance breaches a concentration limit, post-execution monitoring surfaces the breach after the transaction has settled on-chain. For a regulated institution, that sequence means the breach is already in the portfolio by the time the risk committee is notified. Pre-execution validation blocks the transaction before it settles. That is the governance standard applied to every other delegated capital management arrangement in regulated finance.
A compliance log for institutional DeFi purposes should contain a sequential record of every execution decision, the specific mandate parameters checked at the time of each decision, every transaction blocked and the mandate limit that triggered the block, and every protocol interaction, all in a format that can be exported and verified independently by an external auditor. A block explorer provides transaction verification. A compliance log provides mandate verification. The distinction matters for regulatory audit purposes.
Permissioned access addresses whether institutional participants can enter a DeFi protocol in a compliant manner. It does not address whether the governance architecture of the vault itself satisfies institutional due diligence requirements. The three barriers that stop most institutional allocations are the absence of pre-execution mandate controls, the absence of an exportable audit trail, and the absence of contractual role separation. KYC gating and whitelisted pools do not address any of those three requirements.
Société Générale, through SG FORGE, deployed into Morpho protocol vaults following a purpose-built institutional risk framework. Bitwise launched a non-custodial vault on Morpho in January 2026. Anchorage Digital provides institutional clients with access to Morpho Vaults with custody of the resulting vault tokens. Each of these deployments required developing or identifying governance infrastructure that addressed the pre-execution, audit, and role separation requirements that standard vault products do not provide.
P2P.org builds the protection layer that sits between regulated institutions and DeFi execution environments. If you are evaluating the infrastructure requirements, for a DeFi allocation program, talk to our team.on-chain
<p>The start of April 2026 has brought several significant developments across Ethereum staking infrastructure, tokenized asset markets, ETF product evolution, and the convergence of traditional and on-chain finance.</p><p>From the Ethereum Foundation completing a landmark treasury shift to Apollo Global Management deepening its on-chain lending infrastructure commitment, this edition highlights five developments shaping how institutional capital interacts with decentralized networks.</p><p>👉 Subscribe to our newsletter at the bottom of this page to receive a monthly summary of the latest DeFi and staking developments, curated for institutional participants.</p><h2 id="quick-learning-for-busy-readers"><strong>Quick Learning for Busy Readers</strong></h2><ul><li>The Ethereum Foundation has completed its 70,000 ETH staking commitment, shifting from ETH sales to a protocol-native yield model</li><li>Grayscale's Ethereum Staking ETF has operationalized new liquidity mechanics for managing staked asset redemptions</li><li>Tokenized U.S. Treasuries have crossed $12.88 billion in distributed asset value, with represented asset value up 31% in thirty days</li><li>Major financial institutions are actively transitioning parts of the repo market onto blockchain settlement infrastructure</li><li>Apollo Global Management has entered a structured cooperation agreement with Morpho, committing to acquire up to 9% of the protocol's governance token supply over four years</li></ul><p>Missed the previous DeFi Dispatch? Catch up on the latest DeFi news and signals from the previous edition:</p><p>👉 <a href="https://p2p.org/economy/defi-dispatch-defi-news-and-signals-march-2026-issue-2/">https://p2p.org/economy/defi-dispatch-defi-news-and-signals-march-2026-issue-2/</a></p><h2 id="whats-driving-defi-markets-at-the-start-of-april-2026"><strong>What's driving DeFi markets at the start of April 2026?</strong></h2><p>The developments at the opening of April 2026 reflect a market in structural transition. Institutional participants are moving from observing blockchain infrastructure to actively embedding capital within it, whether through staking treasury strategies, ETF product development, on-chain settlement systems, or direct protocol governance positions.</p><p>Below, we break down five key developments and why they matter for asset managers, custodians, hedge funds, ETF issuers, exchanges, and staking teams.</p><h3 id="1-the-ethereum-foundation-completes-its-70000-eth-staking-commitment"><strong>1. The Ethereum Foundation Completes Its 70,000 ETH Staking Commitment</strong></h3><p>The Ethereum Foundation has staked roughly $143 million worth of ether, effectively completing its previously announced 70,000 ETH staking target. The move shifts the foundation from regularly selling ETH to fund its approximately $100 million in annual expenses toward earning a staking yield of an estimated $3.9 million to $5.4 million a year instead.</p><p>The goal is to generate staking rewards to fund protocol research, grants, and operations, replacing the previous practice of selling ETH, which often created sell pressure in the market. The program uses open-source tools for distributed signing and validator management with diverse client pairings for security and decentralization, with no reliance on centralized providers.</p><p>Sources: <a href="https://www.coindesk.com/markets/2026/04/03/ethereum-foundation-stakes-another-usd93-million-ether-reaching-its-70-000-eth-target?ref=p2p.org" rel="noreferrer">CoinDesk</a>, <a href="https://www.tekedia.com/ethereum-foundation-stakes-22517-eth-via-the-treasurys-multisignature-wallet/?ref=p2p.org" rel="noreferrer">Tekedia</a></p><h4 id="why-is-this-important"><strong>Why is this important?</strong></h4><p>This development matters for several interconnected reasons:</p><ul><li>It signals that even the network's own foundation views staking as a preferred capital management mechanism over market liquidations.</li><li>It reduces structural ETH sell pressure from one of the ecosystem's largest treasury holders.</li><li>It demonstrates how large institutional entities can use proof-of-stake mechanics to generate protocol-native yield without relying on centralized staking providers.</li><li>It reinforces the importance of validator infrastructure as the operational layer enabling these treasury strategies at scale.</li></ul><p>For validator operators and staking teams, the Ethereum Foundation's shift models a treasury playbook that asset managers and treasury committees are increasingly considering.</p><h3 id="2-grayscale-ethereum-staking-etf-operationalizes-new-redemption-mechanics"><strong>2. Grayscale Ethereum Staking ETF Operationalizes New Redemption Mechanics</strong></h3><p>Beginning on April 6, 2026, Grayscale's Ethereum Staking ETF introduced new liquidity tools for handling share redemptions when Ethereum liquidity is constrained, including the ability to use delayed delivery orders where digital assets owed to a liquidity provider are delivered once specific staked assets become transferable.</p><p>The formalization of a liquidity provider agreement represents a significant operational milestone, designed to ensure the ETF functions smoothly on NYSE Arca with proper mechanisms for share creation, redemption, and trading. </p><p>Sources: <a href="https://www.stocktitan.net/sec-filings/ETHE/8-k-grayscale-ethereum-staking-etf-reports-material-event-f99833794056.html?ref=p2p.org" rel="noreferrer">Stocktitan</a>, <a href="https://www.minichart.com.sg/2026/04/07/grayscale-ethereum-staking-etf-files-8-k-with-sec-key-details-and-registration-information/?ref=p2p.org">Minichart</a>.</p><h4 id="why-is-this-important-1"><strong>Why is this important?</strong></h4><p>Staking within an ETF structure introduces liquidity management challenges that do not exist in standard spot products. The unbonding period on Ethereum means staked assets cannot be instantly liquidated to meet redemptions. The operationalization of delayed delivery mechanisms is a direct response to this constraint, and its formal codification signals:</p><ul><li>ETF issuers are actively solving the redemption mechanics that staking introduces into regulated product structures.</li><li>Infrastructure decisions at the custody and validator layer directly affect how ETF products perform under redemption pressure.</li><li>As more issuers develop staking-enabled products, these operational frameworks become reference architecture for the broader market.</li></ul><p>For custodians, exchanges, and institutional staking teams, this is the mechanics layer that determines whether staking ETFs scale.</p><h3 id="3-tokenized-us-treasuries-cross-1288-billion-in-distributed-asset-value"><strong>3. Tokenized U.S. Treasuries Cross $12.88 Billion in Distributed Asset Value</strong></h3><p>As of early April 2026, tokenized U.S. Treasuries hold approximately $12.88 billion in total value across distributed and represented assets, having grown from roughly $5 billion in late 2024, reflecting sustained institutional demand. </p><p>Represented asset value across the broader tokenization ecosystem stood at $441.38 billion as of April 6, up 31.61% over the prior thirty days. A joint statement from the Federal Reserve, OCC, and FDIC in Q1 2026 clarified that the capital rule is technology-neutral, meaning an eligible tokenized security receives the same capital treatment as the non-tokenized form of the same security. </p><p>Sources: <a href="https://metamask.io/news/types-of-tokenized-real-world-assets-rwa-categories?ref=p2p.org">MetaMask</a>, <a href="https://www.fintechweekly.com/news/real-world-asset-tokenization-explainer-institutional-2026?ref=p2p.org">FinTech News</a>.</p><h4 id="why-is-this-important-2"><strong>Why is this important?</strong></h4><p>Tokenized government securities are becoming the benchmark low-risk asset for compliant institutional capital on-chain. The growth from $5 billion to nearly $13 billion in roughly 18 months reflects:</p><ul><li>A shift from experimentation to production-scale deployment among asset managers and funds.</li><li>Regulatory guidance providing the framework for banks and asset managers to treat tokenized instruments the same as their non-tokenized equivalents.</li><li>The emergence of programmable treasury management as a genuine institutional tool, not a pilot category.</li></ul><p>As tokenized assets scale, the reliability and security of the blockchain networks settling these instruments becomes increasingly central to institutional risk assessment.</p><h3 id="4-major-financial-institutions-move-repo-market-infrastructure-on-chain"><strong>4. Major Financial Institutions Move Repo Market Infrastructure On-Chain</strong></h3><p>As of April 6, 2026, major financial institutions are actively transitioning parts of the $12.5 trillion repo market onto Ethereum, representing one of the most significant signals of traditional finance embedding blockchain infrastructure into core settlement operations. </p><p>Institutional crypto in 2026 is increasingly centred on controlled access, with large financial firms using on-chain systems for repo, treasury activity, and cash management inside environments built around compliance and permissions, while simultaneously seeking access to the liquidity available on public chains. </p><p>Sources: <a href="https://coinmarketcap.com/cmc-ai/ethereum/latest-updates/?ref=p2p.org">CoinMarketCap</a>, <a href="https://beincrypto.com/on-chain-economy-splitting-in-two/?ref=p2p.org">BeInCrypto</a>.</p><h4 id="why-is-this-important-3"><strong>Why is this important?</strong></h4><p>The repo market is one of the most foundational mechanisms in global finance, functioning as the overnight collateral and liquidity backbone for banks, funds, and financial market participants. Its migration toward blockchain settlement infrastructure signals:</p><ul><li>Blockchain is no longer being evaluated as an alternative to traditional finance, but as the settlement layer for it.</li><li>On-chain settlement for repo creates direct demand for stable, high-performance validator infrastructure to process and finalize transactions reliably.</li><li>As permissioned and public chain environments begin connecting, validator operators supporting public networks become part of the institutional settlement stack.</li></ul><p>For hedge funds, custodians, and treasury teams, this is the convergence point many have been anticipating.</p><h3 id="5-apollo-global-management-enters-structured-cooperation-agreement-with-morpho"><strong>5. Apollo Global Management Enters Structured Cooperation Agreement With Morpho</strong></h3><p>Apollo Global Management struck a cooperation agreement to support lending markets built on Morpho's on-chain protocol. The deal allows Apollo to acquire up to 90 million MORPHO tokens over 48 months, which would represent approximately 9% of the protocol's governance token supply. The move follows BlackRock's push into decentralized finance, listing its tokenized fund and acquiring tokens of decentralized exchange Uniswap. </p><p>The Apollo deal follows several high-profile institutional partnerships that have helped Morpho strengthen its position in decentralized lending. In late January 2026, Bitwise Asset Management introduced its first on-chain vault on Morpho, offering USDC deposits with yields of up to 6%. Morpho currently holds approximately $5.8 billion in total value locked. </p><p>Sources: <a href="https://www.coindesk.com/business/2026/02/15/wall-street-giant-apollo-deepens-crypto-push-with-morpho-token-deal?ref=p2p.org">CoinDesk</a>, <a href="https://crypto.news/apollo-morpho-token-acquisition-defi-lending-2026/?ref=p2p.org">Crypto News</a>.</p><h4 id="why-is-this-important-4"><strong>Why is this important?</strong></h4><p>Apollo managing approximately $940 billion in assets, acquiring a governance stake in a DeFi lending protocol is not a portfolio allocation. It is a structural commitment to on-chain credit infrastructure:</p><ul><li>It signals that alternative asset managers are evaluating DeFi lending protocols as operational infrastructure, not speculative positions.</li><li>The cooperation agreement component, focused on supporting lending markets built on Morpho, means Apollo is embedding its credit expertise directly into on-chain vault design.</li><li>Morpho's curated vault architecture, where professional risk teams allocate capital across isolated lending markets, is increasingly the model that institutions recognize as compatible with their risk management requirements.</li></ul><p>For staking product managers, DeFi infrastructure teams, and risk committees, the Apollo deal is the clearest signal yet that institutional capital is moving beyond observation and into direct protocol-level engagement.</p><h2 id="key-takeaways-for-asset-managers-custodians-hedge-funds-etf-issuers-exchanges-and-staking-teams"><strong>Key Takeaways for Asset Managers, Custodians, Hedge Funds, ETF Issuers, Exchanges, and Staking Teams</strong></h2><p>The start of April 2026 highlights several converging trends:</p><ul><li>Staking is becoming a treasury management tool for major ecosystem participants, not only a validator activity.</li><li>ETF products are operationalizing the liquidity mechanics that staking introduces into regulated structures.</li><li>Tokenized real-world assets are moving from pilot to production at an institutional scale.</li><li>Traditional financial infrastructure, including repo markets, is beginning to settle on blockchain networks.</li><li>Alternative asset managers are acquiring direct governance positions in DeFi lending protocols.</li></ul><p>These developments reinforce how blockchain infrastructure is transitioning from an alternative financial layer to the settlement and operational backbone of institutional capital markets.</p><h2 id="frequently-asked-questions-faqs"><strong>Frequently Asked Questions (FAQs)</strong><br></h2><h3 id="why-is-defi-news-relevant-for-staking-participants"><strong>Why is DeFi news relevant for staking participants?</strong></h3><p>DeFi news reflects how capital flows through blockchain ecosystems. These flows influence staking participation rates, validator demand, and the economic conditions in which staking infrastructure operates.</p><h3 id="what-is-the-repo-market-and-why-does-its-move-on-chain-matter"><strong>What is the repo market,</strong> <strong> and why does its move on-chain matter?</strong></h3><p>The repo market is the mechanism by which financial institutions lend and borrow against collateral on a short-term basis. It underpins global liquidity. When it moves on-chain, it creates direct demand for the blockchain infrastructure that processes and finalizes those transactions.</p><h3 id="are-staking-yields-within-etf-structures-the-same-as-staking-directly"><strong>Are staking yields within ETF structures the same as staking directly?</strong></h3><p>No. ETF staking yields are affected by the proportion of assets staked, unbonding periods, custodian service fees, and the need to maintain liquidity reserves for redemptions. These factors mean ETF staking yields are typically lower than direct on-chain staking yields.</p><h3 id="what-does-tokenized-treasury-growth-mean-for-defi-infrastructure"><strong>What does tokenized Treasury growth mean for DeFi infrastructure?</strong></h3><p>As tokenized Treasuries scale, they require the blockchain networks settling them to maintain high uptime, security, and reliability. Validator infrastructure supporting those networks becomes part of the financial infrastructure stack.</p><h3 id="what-is-a-curated-defi-vault-and-why-are-institutions-interested"><strong>What is a curated DeFi vault, and why are institutions interested?</strong></h3><p>A curated vault is a smart contract managed by professional risk teams that allocates depositor capital across isolated lending markets with defined risk parameters. Institutions are attracted to the combination of on-chain transparency, non-custodial asset control, and structured risk management that curated vaults provide.</p><hr><p>👉 <strong>Subscribe to our newsletter </strong>to receive a monthly summary of the latest DeFi and staking developments, curated for institutional participants. </p><p>👉 <strong>Or follow us on </strong><a href="https://ky.linkedin.com/company/p2p-org?ref=p2p.org" rel="noreferrer"><strong>LinkedIn</strong></a><strong> or </strong><a href="https://x.com/P2Pvalidator?ref=p2p.org" rel="noreferrer"><strong>X</strong></a> to stay updated when new DeFi Dispatch editions are published.</p>
from p2p validator